
Written by: Senior AQA Engineer
Ievgen IevdokymovPosted: 06.05.2026
14 min read
A single misconfigured API endpoint exposed 9.7 million financial records in a 2024 breach affecting a European neobank. No sophisticated exploit. No nation-state attacker. Just an unauthenticated endpoint that never should have been reachable, and a QA process that never thought to check.
Fintech applications sit at the intersection of sensitive personal data, real-time financial transactions, and complex third-party integrations. That combination makes them high-value targets, and it also makes traditional security testing, a pen test before launch, a compliance checklist at year-end, dangerously insufficient.
The answer isn't just more testing. It's a fundamentally different posture: zero-trust QA, where no user, service, or data flow is implicitly trusted, and every security control is continuously verified, not assumed.
This article walks through what that looks like in practice, from the specific vulnerabilities that make fintech apps unique, to a six-pillar testing framework, to how you integrate zero-trust security verification across the full SDLC.
Why fintech apps demand a different security approach
Most software has a relatively contained attack surface. Fintech apps don't. A single application may expose open banking APIs to dozens of third-party providers, process real-time payment flows, store KYC documents, integrate with card networks, and serve users across mobile, web, and embedded interfaces, simultaneously.
Each integration point is a potential entry vector. Each transaction flow carries business logic that, if exploited, can result in direct financial loss, not just a data leak.

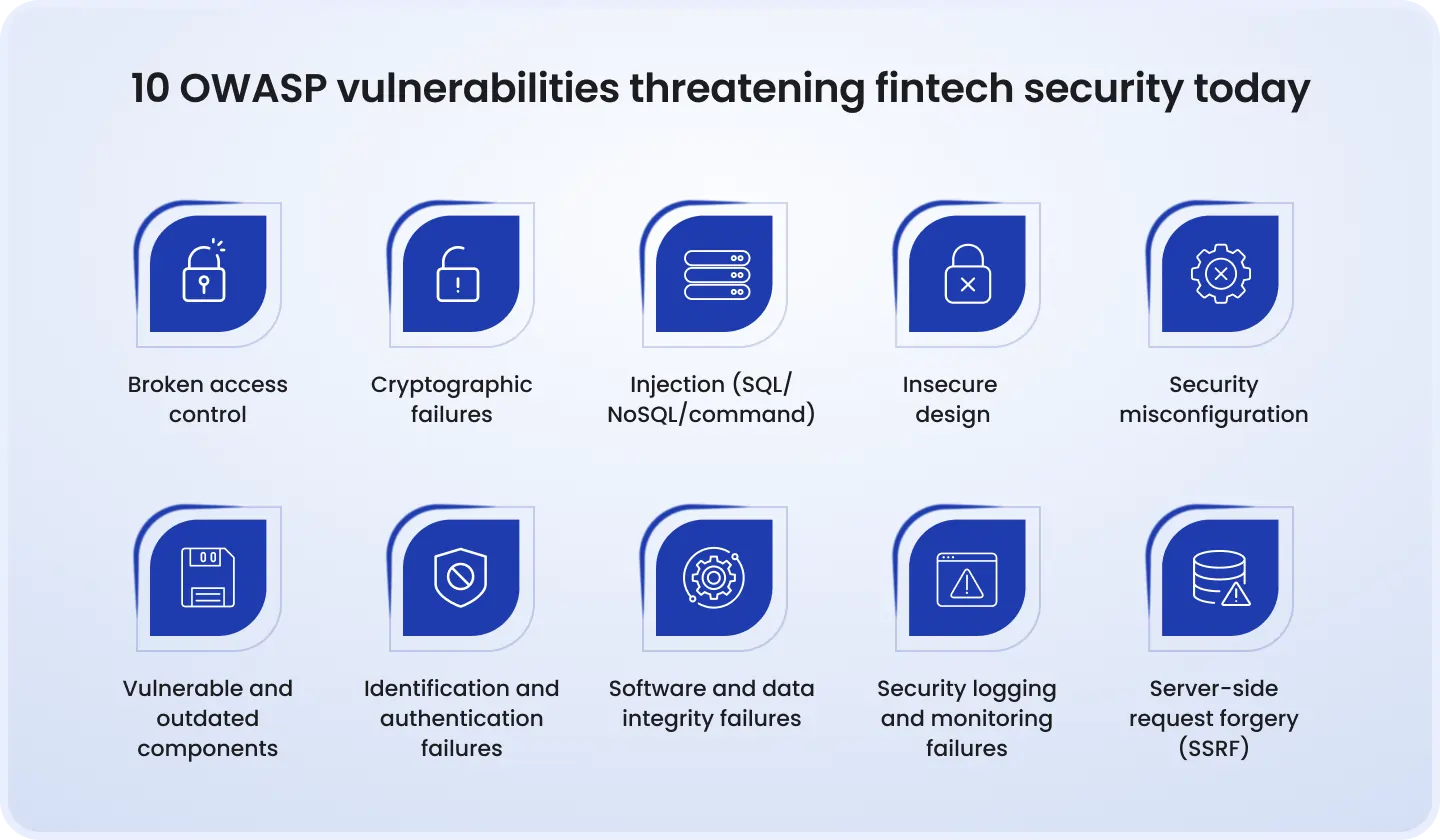
The most common fintech-specific vulnerabilities include:
Race conditions and double-spending, concurrent transaction requests that exploit timing windows to withdraw funds multiple times before a balance update registers
Broken authentication and session integrity, weak token management, missing re-authentication for sensitive operations, or session fixation that allows hijacking
Injection attacks via financial API endpoints, SQL, NoSQL, and command injection in poorly validated API inputs
Rooted/jailbroken device exploitation, apps that fail to detect compromised device environments, exposing locally cached credentials or transaction data
The regulatory stakes compound the risk. PCI DSS mandates specific encryption and access control requirements. GDPR enforces strict rules on PII handling. DORA, the EU's Digital Operational Resilience Act, now requires fintech firms to conduct regular ICT risk testing and demonstrate incident response readiness. A security failure isn't just a breach; it's a compliance event with seven-figure penalty exposure.
There's also an underappreciated insider threat dimension. Employees and third-party vendors with over-provisioned access represent a significant attack surface that perimeter-based security never adequately addresses.
Fintech apps aren't just software. They're financial infrastructure. And QA strategy needs to be built with that weight in mind.
What zero-trust means in a QA context
Zero-Trust Architecture (ZTA) operates on a single governing principle: never trust, always verify. No user, device, or service is trusted by default, regardless of whether they're inside or outside the network perimeter.
Translated into QA, this means:
Verify explicitly, every identity claim, every API call, every device state must be authenticated and tested, not assumed correct
Use least-privilege access, tests must confirm that access controls enforce minimum necessary permissions at every layer
Assume breach, test design must simulate adversarial conditions, not just validate expected behavior
This is a meaningful departure from how most QA teams approach security. Traditional security testing is often perimeter-focused and episodic, a pen test scheduled quarterly, a vulnerability scan run before a major release. Zero-trust QA is continuous and embedded. It asks not "is the perimeter secure?" but "if the perimeter was already breached, would our controls hold?"
For fintech specifically, this matters because modern architectures have no meaningful perimeter. Microservices communicate over internal APIs. Cloud infrastructure is shared. Third-party SDKs run inside your app. The implicit trust relationships in these systems are exactly where attackers look, and exactly where QA needs to go.
Learn how we turned a broken QA process into a scalable testing system
The zero-trust QA framework: 6 core testing pillars
Pillar 1: Identity & access management (IAM) testing
IAM is the first line of zero-trust enforcement, and one of the most frequently under-tested areas in fintech QA.
Testing here goes beyond confirming that a login page works. It means:
Verifying that MFA is enforced for all sensitive operations, not just initial login
Confirming that RBAC boundaries are actually enforced, a customer service agent shouldn't be able to access another user's full transaction history even if they know the account ID
Testing privilege escalation paths: can a standard user manipulate API parameters to access admin-level endpoints?
Validating token lifecycle management, expiry, rotation, revocation, and re-authentication requirements for high-risk actions like fund transfers
Realistic scenario: A QA team discovers that password reset tokens don't expire after use. An attacker who intercepts a reset link once (e.g., through email forwarding) can reuse it indefinitely. This class of bug is trivial to find, but only if your tests explicitly check it.
Tools like Burp Suite and OWASP ZAP are standard for session manipulation and token testing. Complement them with manual exploratory testing for privilege escalation scenarios that automated scanners miss.
Pillar 2: API security testing
APIs are the dominant attack surface in fintech. Open banking regulations have accelerated API proliferation, and with it, the exposure.
The OWASP API Security Top 10 is the mandatory baseline. The most critical fintech-specific concerns:
Broken Object Level Authorization (BOLA), an authenticated user queries
/api/accounts/12345and can substitute any account ID to access another user's dataMass assignment, API endpoints that accept full object payloads may allow attackers to set fields (e.g.,
isAdmin: true) that shouldn't be user-controllableImproper rate limiting, without throttling, attackers can enumerate accounts, brute-force OTPs, or perform credential stuffing at scale
In microservice architectures, east-west traffic (service-to-service) is as important as north-south (user-to-app). Test mutual TLS between services. Validate signed request integrity. Confirm that an internal service cannot be called directly from the outside.
Security regression tests for APIs should be automated and run on every build. Any deployment that changes an API contract should trigger a full security re-validation, not just functional checks.
Pillar 3: Transaction flow & business logic testing
Business logic vulnerabilities are the hardest class of bugs to detect, and in fintech, they're the most directly monetizable for an attacker.
Automated scanners can't find a race condition in a payment flow. They don't understand that initiating two simultaneous withdrawal requests against the same balance is an exploit, not just a load test scenario. This requires deliberate, adversarial test design.
Critical test scenarios include:
Double-spending: two simultaneous requests against the same account balance, does the system enforce atomic transactions?
Balance manipulation: what happens if a payment confirmation is delayed and a second transaction is initiated in the window?
Mid-flow interception: can a transaction be modified after user authorization but before processing completes?
Negative balance testing: does the system correctly reject or handle edge cases where calculated balances would go below zero?
Pillar 4: Data encryption & storage validation
Encryption is frequently implemented but rarely tested with rigor. Having AES-256 in your architecture diagram is not the same as verifying it works correctly in every state.
Testing should cover:
Data at rest: confirm that all sensitive fields (PII, card data, account numbers) are encrypted in databases and file storage, not just the obvious ones
Data in transit: validate TLS 1.3 across all connections, including internal microservice communication; test for protocol downgrade attacks
Key management: verify that encryption keys are rotated on schedule, stored in an HSM or equivalent, and that key access is logged and audited
Log sanitization: confirm that sensitive data never appears in plaintext in application logs, a surprisingly common finding in fintech QA audits
Backup encryption: backups are a frequent target; validate that backup data is encrypted and that restore processes maintain access controls
A useful test: spin up a debug environment and attempt to extract data from the database directly, bypassing the application layer. If sensitive data is visible, encryption at rest isn't implemented correctly.
Pillar 5: Device & endpoint security testing
For mobile fintech apps, payments, digital banking, investment platforms, the device is the endpoint, and it cannot be trusted implicitly.
Key tests in this pillar:
Rooted/jailbroken device detection: the app should detect a compromised device environment and restrict or terminate the session; test that this detection cannot be bypassed with common tools
Certificate pinning: verify that the app rejects connections from untrusted certificates, preventing man-in-the-middle attacks; test against common bypass techniques
Biometric authentication fallback paths: if biometric auth fails, does the fallback path maintain the same security level, or does it introduce a weaker route?
Sensitive data in memory: test for sensitive data (tokens, card numbers) persisting in app memory beyond necessary lifecycle
Clipboard and screenshot protection: financial data should not be copyable to clipboard or visible in app switcher screenshots
Research consistently shows that a significant share of mobile app attacks exploit poor endpoint security rather than infrastructure vulnerabilities. Endpoint testing is non-negotiable for any fintech app with a mobile surface.
Pillar 6: Continuous monitoring & anomaly detection validation
Zero-trust is not a configuration you set once. It's a runtime posture, and that means your monitoring and detection systems are themselves a QA responsibility.
Testing in this pillar means actively validating that your security controls fire when they're supposed to:
Simulate unusual login patterns: logins from new geographies, impossible travel scenarios, multiple failed MFA attempts, do they trigger the correct alerts?
Abnormal transaction volumes: inject synthetic data representing unusual activity (e.g., 500 microtransactions in 60 seconds) and confirm fraud detection responds correctly
Lateral movement simulation: test whether a compromised service account can move between microservices beyond its authorized scope
Alert-to-remediation validation: does a detected anomaly actually trigger the documented incident response workflow, or does it just write to a log file no one reads?
This pillar is where many fintech security programs have the largest gap. Detection capabilities are built but never stress-tested. The first real validation ends up being an actual incident.

Integrating zero-trust security testing into the SDLC
Zero-trust QA only works if it's embedded across the development lifecycle, not bolted on before release.
Design
Threat modeling
Assume breach mindset
Development
SAST, dependency scanning
Least-privilege, known vulnerabilities
Testing
DAST, API security tests
Explicit verification, auth controls
Production
Continuous monitoring validation
Real-time anomaly detection
Shift-left security means introducing security thinking at the requirements stage. Before a new payment feature is designed, ask: what are the abuse cases? What would an attacker do with this flow? Threat modeling sessions at the design phase cost a fraction of what remediation costs post-deployment.
SAST integrates into developer workflows, scanning code for injection flaws, insecure dependencies, and hardcoded credentials before it ever leaves a developer's branch. DAST validates the running application, catching runtime vulnerabilities that static analysis misses.
Learn how we built a reliable QA system for a growing fintech product
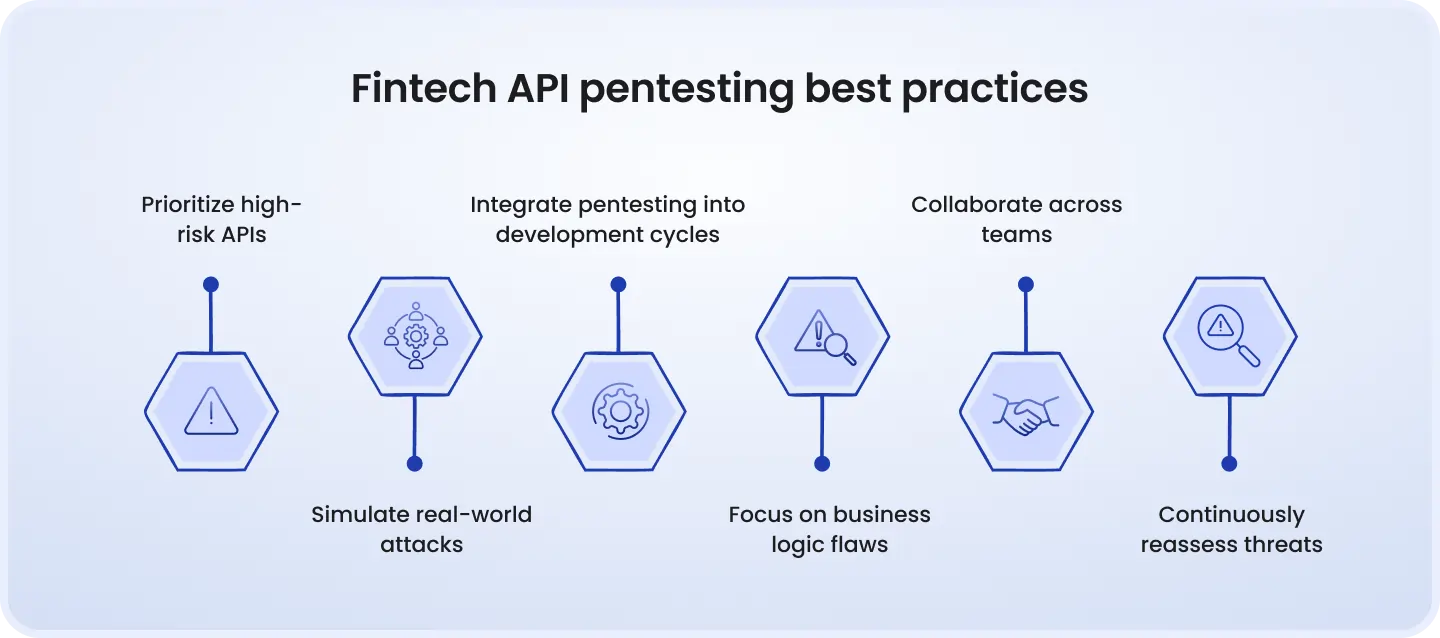
Penetration testing should follow a structured framework, OWASP Top 10, MITRE ATT&CK, NIST SP 800-115, and be conducted at least annually, or after any significant architectural change. Red team and purple team exercises go further, simulating realistic attack chains to validate whether zero-trust controls hold under adversarial conditions.
Security regression testing in CI/CD pipelines is the mechanism that makes all of this continuous. Every code push should trigger automated security checks. Security becomes a gating criterion, not a final review step.
Key compliance checkpoints in your zero-trust QA strategy
Compliance frameworks and zero-trust QA overlap significantly, but they're not the same thing, and conflating them creates a false sense of security.
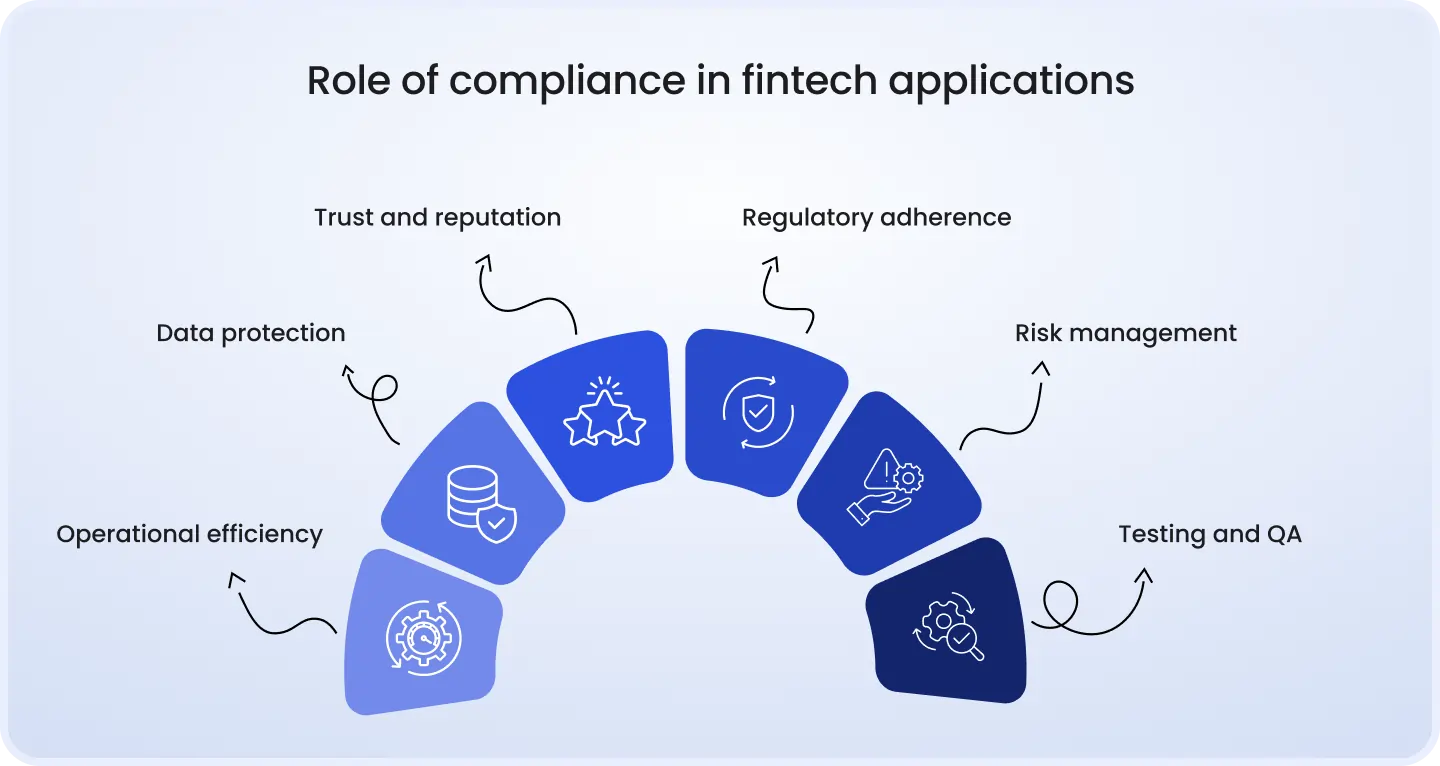
PCI DSS: mandates encryption standards, access control requirements, and regular penetration testing for any application that handles card data. Your zero-trust framework should map directly to PCI DSS controls, and your test evidence should be audit-ready
GDPR: requires that PII handling be tested explicitly, data minimization, purpose limitation, and the right to erasure all have testable implementations
DORA: the EU's operational resilience regulation requires ICT risk testing, threat-led penetration testing (TLPT) for significant institutions, and documented incident response validation, all of which align directly with zero-trust QA practices
The practical advantage of zero-trust QA for compliance: continuous testing produces continuous evidence. When a regulator asks for your security posture, you have test logs, not assurances.
The important caveat: passing a compliance audit does not mean your application is secure. PCI DSS compliance has coexisted with major card data breaches. Zero-trust QA goes beyond checkbox validation to actual adversarial resilience.
Common zero-trust QA mistakes to avoid
Even well-resourced fintech QA teams make the same recurring errors:
Treating security as a pre-launch gate, a single pen test before release doesn't validate zero-trust; it validates a point-in-time snapshot of a static codebase
Testing only happy paths, security vulnerabilities almost always live in edge cases, error states, and unexpected input combinations
Ignoring third-party integrations, payment gateways, KYC providers, and analytics SDKs are trusted by default and tested almost never; they're a live attack surface
Over-relying on automated tools, scanners catch known patterns; business logic vulnerabilities, authorization flaws, and race conditions require manual, adversarial thinking
Siloing security from QA, zero-trust requires that security engineers, QA engineers, and developers share context; security findings that don't reach QA regression suites get refound every cycle
Skipping incident response testing, anomaly detection that alerts but doesn't trigger remediation is not a security control; it's a notification system
Conclusion
Security is not a product feature or a compliance deliverable. It's the foundation that makes everything else viable, user trust, regulatory standing, and the ability to scale without catastrophic exposure.
Zero-trust QA is the operational model that matches the threat environment. It doesn't assume any component is safe. It doesn't compress security into a pre-release sprint. It embeds adversarial thinking into every stage of development, from threat modeling in design to anomaly detection validation in production.
The shift is organizational as much as technical. QA teams need to think like attackers. Security teams need to think like QA engineers. And both need to share ownership of a testing pipeline that treats every trust relationship in the system as something to be earned through evidence, not assumed.
For fintech companies building or scaling this capability, the path starts with the six pillars: IAM, API security, transaction logic, encryption, device security, and monitoring validation. Map your current test coverage against each. The gaps you find are your roadmap.
DeviQA provides specialized security testing services for fintech applications, from API security audits and penetration testing to full zero-trust QA strategy design and implementation. Contact our team to assess your current security testing coverage.
Your dev team need a solid QA partner

About the author
Senior AQA engineer
Ievgen Ievdokymov is a Senior AQA Engineer at DeviQA, focused on building efficient, scalable testing processes for modern software products.