
Written by: Senior AQA Engineer
Ievgen IevdokymovPosted: 01.05.2026
22 min read
A practical guide for QA leads, CTOs, and engineering leaders building reliable, secure, and compliant financial products.
A single miscalculated interest rate. A payment that goes through twice. An API that leaks transaction data under load. In fintech, the consequences of software defects aren't measured in user frustration, they're measured in regulatory fines, customer losses, and brand damage that takes years to repair.
Software failures cost the global economy over $1.7 trillion per year. In financial services, that figure is disproportionately high: a 2023 report by the Bank of England found that IT and cyber incidents were the leading source of operational risk events across major financial institutions.
This guide is written for engineering and product leaders who are building or scaling fintech products and want to understand what a mature QA function actually looks like in this domain, not in theory, but in practice. We'll cover what makes fintech testing different, which areas require dedicated strategies, and how to build a QA approach that keeps pace with both fast release cycles and evolving regulatory requirements.
Why fintech testing is different from standard QA
Most software bugs are recoverable. A broken UI component, a misconfigured API endpoint, or a slow page load can cause frustration, but they rarely threaten a user's finances or a company's legal standing. In fintech software testing, the stakes are much higher, because even a small defect can lead to financial loss, compliance exposure, or serious security risks.
This changes the entire posture of your QA function. Here's what makes fintech testing categorically different:
1. Zero tolerance for calculation errors
Financial software operates on precision. A rounding error in a loan amortization calculation, applied at scale across tens of thousands of accounts, creates both a financial liability and a compliance violation. QA teams must go beyond 'does it work?' and validate that it works correctly to the level of precision that financial regulations require.
2. Regulatory compliance is a QA responsibility
Compliance in fintech isn't a checkbox at the end of development, it's a core part of fintech software testing. QA teams must validate that features behave correctly under PCI DSS, GDPR, PSD2, AML, and KYC requirements. Gaps in compliance validation don't just create technical debt; they lead to audit findings and real regulatory exposure.
3. Complex, high-risk integration ecosystems
Fintech products rarely operate in isolation. They integrate with core banking systems, payment gateways, credit bureaus, identity verification providers, and often multiple third-party APIs simultaneously. Each integration point is a failure surface, and a failure doesn't just break a feature, it can corrupt transaction state or expose sensitive data.
4. Volume, velocity, and concurrency
Payment platforms process millions of transactions per day. Neobanks see usage spikes on paydays. Trading platforms can see order volume increase tenfold in minutes during market volatility. Performance testing in fintech must simulate these real-world load patterns, not just validate that the system works under average traffic.
5. A permanent threat landscape
Financial applications are among the highest-value targets for attackers. Security testing in fintech must be continuous, not a one-time penetration test before launch. Threat models evolve, and so must your QA coverage.
6. Trust is the product
Users entrust fintech applications with their savings, income, and financial identity. A single publicly disclosed security breach or data loss event can destroy the user trust that took years to build. QA is not just about preventing bugs, it's about protecting the company's core value proposition.
Types of fintech applications and their QA implications
Not all fintech products carry the same risk profile. Testing a BNPL feature embedded in an e-commerce app requires a different approach than validating an institutional trading platform. That's why best practices for testing fintech apps safely start with correctly identifying the application type, as it drives every downstream QA decision.
Digital banking and neobanks
These products replace or complement traditional bank accounts. Key testing areas include account management workflows, real-time payment rails (SEPA, Faster Payments, SWIFT), multi-currency balances, card management, and KYC/AML compliance flows. The critical risk: transaction accuracy at scale and regulatory audit trails.
Payment processing platforms
Whether B2B or B2C, payment platforms must guarantee transaction integrity across the full payment lifecycle, authorization, capture, settlement, refund, and dispute handling. QA coverage must include edge cases like partial captures, network timeouts, and double-spend prevention. Compliance focus: PCI DSS across all cardholder data touchpoints.
Learn how we cut regression testing time by 2× for a global payment platform
Lending and credit applications
These products calculate credit scores, originate loans, and manage repayments. Business logic testing is paramount: interest calculations, fee structures, early repayment penalties, and delinquency workflows must all behave correctly under a wide range of input conditions. A miscalculation in APR disclosure is a regulatory violation in most jurisdictions.
Investment and trading platforms
Speed and accuracy are non-negotiable. Order routing, execution logic, portfolio valuation, and reporting must all be tested under both normal and extreme market conditions. Performance testing must simulate market open spikes, flash crash scenarios, and burst order flow. Regulatory scope: MiFID II, SEC reporting requirements.
Insurtech
Policy underwriting logic, claims processing workflows, and premium calculation engines all require deep functional testing. Integration testing with external data providers (weather APIs, telematics platforms, medical databases) adds significant complexity.
Embedded finance and BNPL
These products live inside third-party host applications, which means QA must account for the host's tech stack, integration contracts, and user journey context. BNPL specifically requires testing credit decisioning at checkout speed, often in under two seconds, alongside repayment scheduling and delinquency triggers.
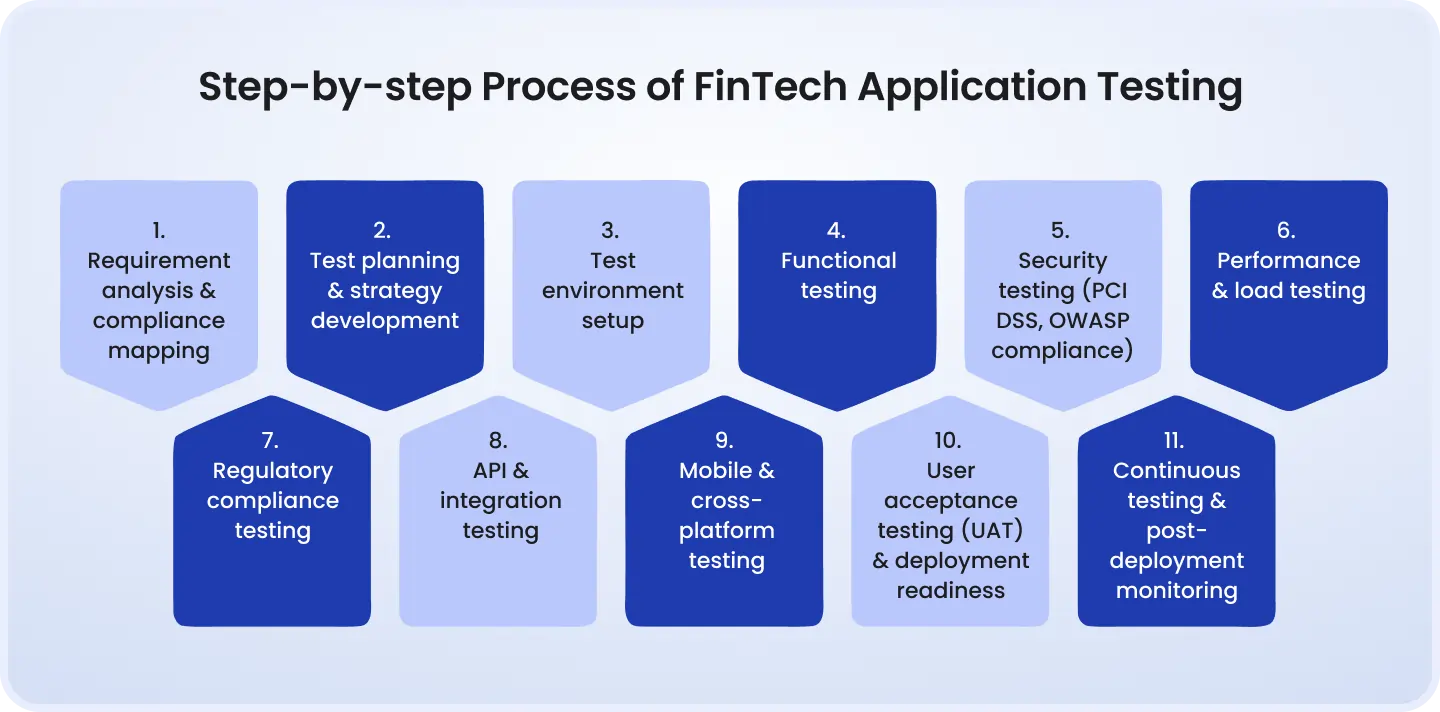
Core areas of fintech QA testing

1. Functional testing
Functional testing in fintech goes beyond confirming that a feature works as specified. It requires validating that every business rule, often embedded in regulatory requirements, behaves correctly across all relevant input conditions, edge cases, and failure scenarios.
Key focus areas include:
Transaction accuracy and calculation logic, interest, fees, exchange rates, rounding behavior
End-to-end user flows, onboarding, KYC submission, identity verification, payments, withdrawals, account closure
Edge cases, what happens when a payment fails mid-authorization? When a user submits KYC documents in an unsupported format? When a refund is requested on a partially settled transaction?
Business rule validation, credit limits, transaction caps, fraud thresholds, rate limits, fee triggers
A practical example: testing a currency exchange feature requires not just confirming that the rate is displayed and the trade executes, it requires validating that the rate used matches the contracted rate at the time of execution, that the correct fees are applied, and that the transaction record reflects the exchange rate snapshot for audit purposes.
2. Security testing
Security testing in fintech cannot be treated as a periodic event. It must be an ongoing discipline embedded into the development lifecycle, with dedicated coverage across authentication, authorization, data handling, and external attack surfaces.
Core security testing areas:
OWASP Top 10 for financial applications, injection, broken authentication, sensitive data exposure, insecure deserialization, and others specific to financial API surfaces
Penetration testing, structured adversarial testing of the application's external attack surface, ideally conducted by an independent team on a quarterly or release-triggered cadence
Authentication and session management, token expiry, multi-factor authentication flows, session fixation, privilege escalation paths
Data encryption validation, confirming that sensitive data (card numbers, account details, PII) is correctly encrypted at rest and in transit, and that keys are managed appropriately
Fraud detection logic validation, testing that fraud rules trigger correctly, that legitimate transactions aren't falsely flagged, and that the system responds appropriately when rules fire
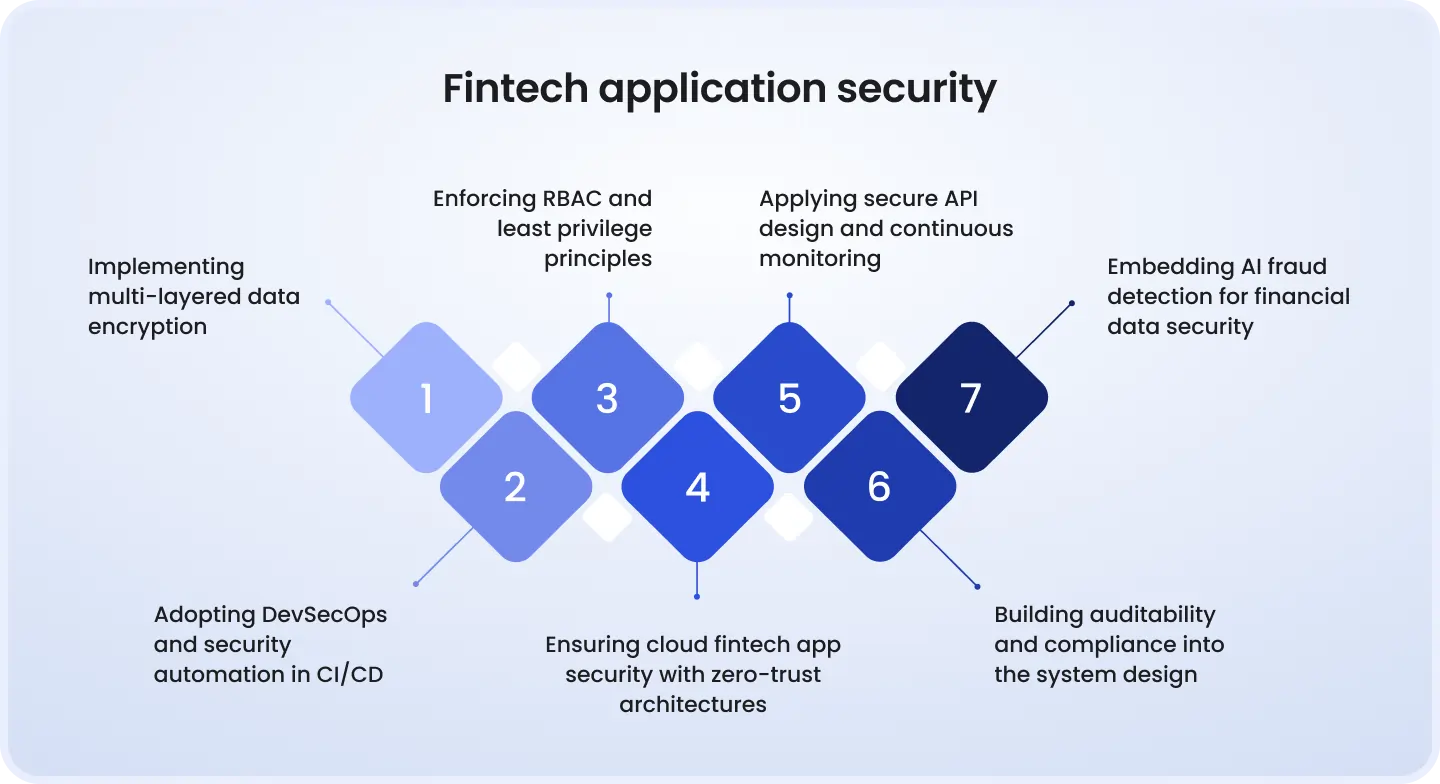
A common gap in fintech security testing: teams validate that security controls exist, but don't test whether they can be bypassed. Penetration testing and negative testing scenarios, attempting to break the controls, are essential to a complete security posture.
3. Compliance testing
Compliance testing validates that the application behaves according to the specific requirements of applicable regulations. This is distinct from functional testing, it's not just about what the system does, but whether what it does meets a regulatory standard that an auditor or regulator will scrutinize.
Key compliance testing domains:
PCI DSS, cardholder data environment scoping, network segmentation validation, encryption of card data, access control testing, audit log completeness
GDPR / data privacy, right to erasure verification, data minimization validation, consent recording and withdrawal, cross-border transfer controls
PSD2 / Open Banking, strong customer authentication (SCA) flows, API access controls for third-party providers, transaction history access rights
AML and KYC workflows, validation that customer due diligence checks fire at the correct thresholds, that suspicious activity reports are generated correctly, and that watchlist screening is current and accurate
Audit trail and logging, confirming that all regulated events are logged with correct timestamps, actor IDs, and record integrity
An important distinction: compliance testing doesn't replace a formal audit, but it dramatically reduces the risk of findings during one. Teams that build compliance test suites aligned to their regulatory obligations can demonstrate a testing paper trail that auditors value highly.
4. Performance and load testing
Fintech systems must perform under the conditions that real usage creates, not average load, but peak load. A payment platform that processes 10,000 transactions per minute on a normal Tuesday may face 80,000 per minute on Black Friday. The QA question isn't 'does it work?', it's 'does it hold?'
What performance testing must cover:
Peak volume simulation, model actual traffic patterns using production metrics, not arbitrary numbers
Latency thresholds, real-time payments typically require sub-second response times; define SLAs and test against them
Scalability validation, confirm horizontal scaling behavior and identify the point at which the system degrades
Stress testing, push the system past expected limits to understand failure modes and confirm graceful degradation
Recovery testing, validate that the system recovers correctly from failure states without data loss or transaction corruption
Case study: Payment platform, performance testing before a product launch
Challenge: A payments startup preparing to launch a consumer-facing product had conducted only basic functional testing. Load testing was planned as a post-launch activity. Their peak transaction estimate was 5,000 per minute.
Solution: A pre-launch load testing engagement simulated 3x the projected peak volume, with realistic transaction mix (authorizations, captures, refunds) and concurrent API integrations. Database query bottlenecks and a connection pool exhaustion issue were identified under sustained load of 8,000 TPS.
Result: Both issues were resolved before launch. The product handled a 400% traffic spike on launch day without degradation. Estimated cost of a production failure at that scale: reputational damage, potential regulatory inquiry, and emergency remediation, conservatively $200K+.
5. Integration testing
Fintech products typically depend on 5–15 third-party integrations: payment gateways, banking rails, identity providers, credit bureaus, fraud platforms, and more. Each integration introduces risk that unit tests and functional tests won't catch.
Integration testing must address:
Payment gateway integrations, authorization flows, settlement timing, error code handling, timeout behavior, partial authorization responses
Core banking system connections, balance synchronization, statement generation, transaction posting latency
Third-party API reliability, what happens when a credit bureau API returns a timeout? Does the system degrade gracefully, queue the request, or fail silently?
Open banking API validation, conformance to API standards, correct data scoping, consent flow accuracy
Contract testing, validating that your service's expectations of a third-party API match that API's actual behavior, independent of end-to-end integration tests
Contract testing tools like Pact allow teams to decouple integration testing from third-party sandbox availability, a significant efficiency gain when external sandboxes are slow, unreliable, or expensive to access.
6. UI/UX and accessibility testing
In financial services, a confusing user interface isn't just a UX problem, it creates compliance risk. Unclear fee disclosures, ambiguous consent flows, and non-accessible interfaces can all generate regulatory scrutiny, particularly under consumer protection frameworks.
Testing requirements:
Cross-platform and cross-browser coverage, financial apps serve diverse user bases; coverage must include iOS, Android, and major desktop browsers
WCAG 2.1 compliance, financial services have specific accessibility obligations in many jurisdictions; automated and manual accessibility testing should both be in scope
Mobile-specific testing, biometric authentication, deep linking, push notification flows, and offline state handling all require platform-specific test coverage
Usability validation on critical flows, onboarding, KYC submission, and payment flows should be tested with real users to identify cognitive friction that leads to drop-off or error
Building a fintech QA strategy: Key principles
The difference between a reactive QA function and a mature one isn't test coverage numbers, it's whether QA is embedded in the development process or bolted onto it at the end. In fintech, the latter approach is untenable given the risk profile.
Principle 1: Risk-based testing
Not all features carry equal risk. A profile picture upload function and a cross-border payment execution engine are not equivalent QA challenges. Risk-based testing means allocating QA effort, depth of coverage, frequency of testing, type of testing, proportionally to the risk a given component carries.
A practical framework: score each module against three axes, financial impact of failure, regulatory exposure, and frequency of change. High scores on all three (e.g., payment processing core) get exhaustive coverage. Low scores on all three get lighter coverage. This ensures QA effort is concentrated where it matters.
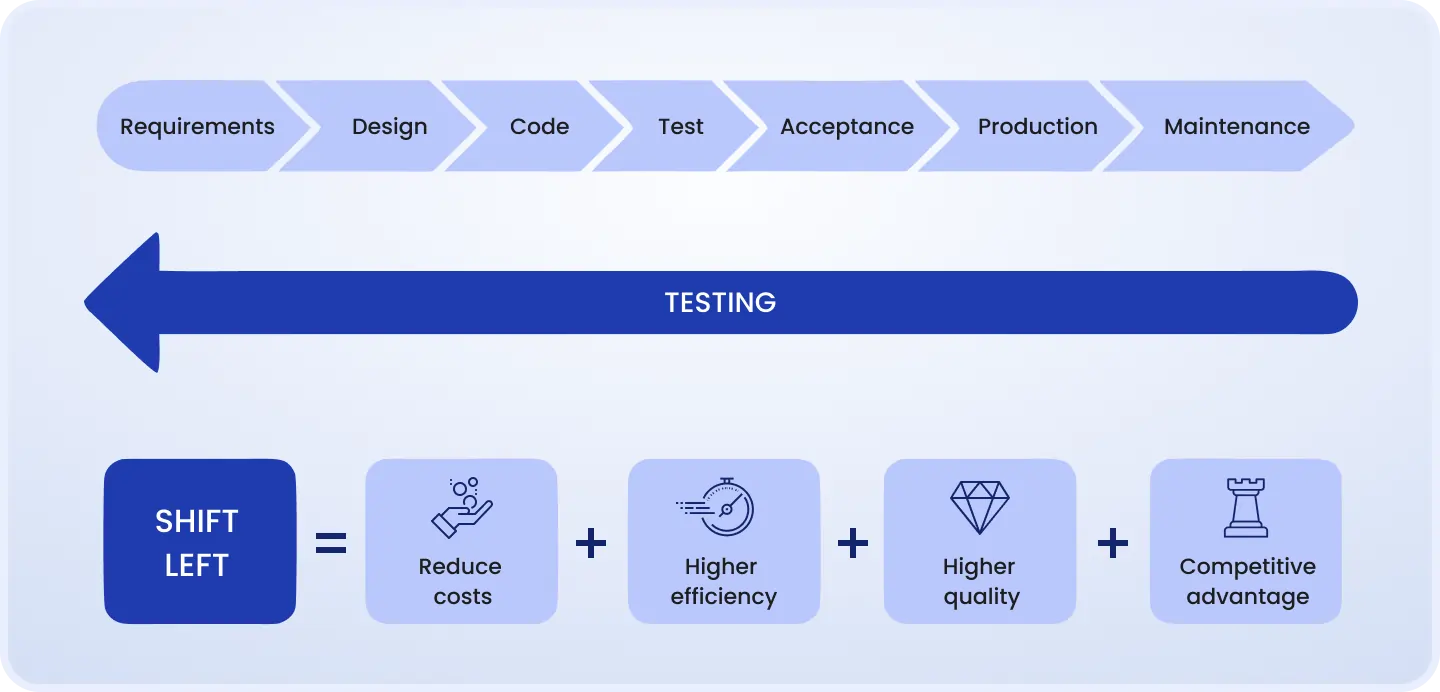
Principle 2: Shift-left testing
Defects found in production cost 6–10x more to fix than defects found during development, and in fintech, the cost multiplier can be far higher when regulatory and reputational factors are included. Shifting QA left means involving QA engineers from the requirements stage, reviewing acceptance criteria, identifying ambiguities, and creating test cases before code is written.
Principle 3: Compliance-first mindset
Compliance requirements should be baked into test cases from the start, not reviewed at the end of a sprint. When a new feature is scoped, QA engineers should identify the regulatory requirements it touches and write compliance validation steps alongside functional ones.
Principle 4: Continuous testing in CI/CD
Fintech teams that release frequently, and most modern fintech teams do, must run automated tests on every commit. Regression suites, smoke tests, API contract tests, and security scans should all run as part of the CI/CD pipeline, with failure gates that prevent deployment if critical tests fail.
Learn how we turned a broken QA process into a scalable testing system
Principle 5: Balance automation and manual testing
Automation covers regression, volume, and consistency. Manual testing covers judgment, exploration, and nuance. In fintech, manual exploratory testing by experienced QA engineers, who understand both the domain and the regulatory context, remains essential and cannot be fully automated away.
Principle 6: QA from requirements, not pre-release
The most common structural failure in fintech QA is treating it as a release gate rather than a continuous discipline. QA engineers should be present in backlog refinement, sprint planning, and architecture reviews, not just in the final days before a release.
Test automation in Fintech application testing
Test automation in fintech has a specific scope and a specific set of limitations. Understanding both is essential to building an automation strategy that actually reduces risk rather than providing false confidence.
What to automate
Regression suites: all previously validated scenarios that must remain working as the codebase evolves
Smoke tests: critical path validation run on every deployment to confirm the system is operational
API tests: contract validation, response format checking, error handling, and performance assertions for all internal and external API integrations
Data validation: automated checks that transaction records, balances, and audit logs are correct after complex operations
Security scans: SAST, DAST, and dependency vulnerability scanning integrated into the pipeline
What to keep manual
Exploratory testing: finding defects that test scripts didn't anticipate, particularly in new or complex features
UX review: evaluating whether the interface actually serves users well, beyond technical correctness
Compliance audits: reviewing whether regulatory requirements are met requires human judgment and domain expertise
Edge case investigation: following threads found in logs, monitoring, or user reports that require contextual reasoning
Recommended tools and frameworks
UI automation: Playwright or Selenium for web; Appium for mobile
API testing: Postman / Newman for exploratory and CI; REST-assured for Java stacks
Performance testing: k6 or Gatling for developer-friendly load testing; JMeter for teams with existing investment
Security scanning: OWASP ZAP for DAST; SonarQube for SAST; Snyk for dependency scanning
Contract testing: Pact for consumer-driven contract testing between microservices
Fintech-Specific Automation Challenges
Three challenges recur consistently in fintech automation environments:
Test data management is the most common blocker. Real financial data cannot be used in test environments due to privacy regulations, but synthetic data must be realistic enough to trigger the business logic you're testing. Invest in a test data management strategy early, retrofitting it is expensive.
Sandbox environment reliability is a persistent problem when testing third-party integrations. External sandboxes go down, behave differently from production, and may not support all scenarios. Service virtualization and mocking are essential tools to decouple your automation from external dependencies.
Test flakiness in financial workflows, particularly those involving asynchronous operations like payment settlement, is harder to manage than in standard web applications. Build explicit wait strategies and idempotency checks into your test design.
Case study: Neobank, automation coverage expansion
Challenge: A European neobank had 23% automated test coverage of its regression suite. Each release required 8–10 days of manual QA, creating a release velocity bottleneck that was slowing feature delivery and frustrating engineering leadership.
Solution: A structured automation buildout prioritized the payment flows, onboarding, and account management modules, covering 80% of the highest-risk user journeys. Playwright was selected for UI coverage; Pact was introduced for API contract testing across 6 internal microservices. A test data factory was built to generate compliant synthetic customer and transaction records.
Result: Regression cycle dropped from 10 days to 3 hours for automated suites, with 2 days of residual manual exploratory testing. Release velocity increased from monthly to bi-weekly. Three compliance-related defects were caught in CI that would previously have reached UAT or production.
Fintech QA challenges and how to address them
The following table summarizes the most common structural challenges in fintech QA, why they arise, and how mature teams address them:
Test data management
Real financial data is PII-regulated and can't be used in non-production environments
Build a synthetic data generation pipeline; implement data masking for production snapshots used in staging
Regulatory changes
Compliance requirements evolve and vary by jurisdiction; keeping test suites current is operationally expensive
Assign compliance monitoring ownership; design modular test suites that map to specific regulatory clauses and can be updated independently
Third-party API instability
External APIs in sandboxes behave differently from production; outages block testing
Use service virtualization and consumer-driven contract testing to decouple from live third-party dependencies
Speed vs. thoroughness
CI/CD release cadence conflicts with the depth of QA fintech requires
Apply risk-based prioritization; automate the high-frequency, high-confidence tests and focus manual effort on high-risk, high-change areas
Security coverage gaps
Security testing is often treated as a separate activity rather than part of QA
Integrate SAST, DAST, and dependency scanning into CI; conduct quarterly penetration testing; include security scenarios in functional test cases
Distributed team coordination
QA, development, compliance, and security teams often work in silos
Establish shared ownership of quality metrics; include QA in architecture reviews and compliance discussions; create shared test environments and reporting dashboards
Fintech QA metrics that actually matter
Test coverage percentage is a misleading headline metric. A system can have 90% code coverage and still miss the business logic errors that matter most. In fintech, QA metrics should reflect risk reduction and operational quality, not just testing activity.
Defect Escape Rate
Percentage of defects found in production vs. testing
In fintech, production defects carry financial, regulatory, and reputational cost; this rate must be tracked by severity and module
Compliance Audit Pass Rate
Percentage of compliance test cases passing against current requirements
Direct indicator of regulatory exposure; a failing compliance test suite is an audit risk
Mean Time to Detect (MTTD)
Time from defect introduction to discovery
Lower MTTD means defects are caught earlier in the cycle, when they're cheapest to fix
Mean Time to Resolve (MTTR)
Time from defect detection to production fix
Tracks the efficiency of the full defect response cycle, including triage, fix, and regression
Regression Suite Stability
Percentage of automated test runs that pass without flakiness
High flakiness erodes trust in automation and leads teams to ignore failures, dangerous in a fintech context
Security Vulnerability Detection Rate
Vulnerabilities found in QA vs. found in production or by external reports
Tracks whether your security testing program is catching issues before attackers do
One often-overlooked metric: test coverage mapped to compliance requirements. This tracks not just how many tests you have, but whether every regulatory obligation has validated test coverage. For teams subject to PCI DSS, GDPR, or PSD2, this mapping is also valuable documentation for audit purposes.
Choosing the right QA partner for fintech
The decision between in-house QA and an external QA partner in fintech is rarely binary. Most mature fintech organizations operate a hybrid model: a core in-house QA function responsible for strategy, compliance knowledge, and institutional context, supplemented by an external partner for specific capacity needs, specialist testing services (penetration testing, performance testing), or accelerating automation buildout.
In-house vs. outsourced QA
In-house QA strengths, deep product knowledge, regulatory context, integration into sprint cadence, cultural alignment, and continuity across releases
Outsourced QA strengths, faster scaling, access to specialized skills (security testing, performance engineering, automation), independent perspective, and cost efficiency for non-core testing activity
The hybrid model, maintain in-house QA ownership of strategy and compliance; leverage external partners for capacity, specialization, and independent audit functions
What to look for in a fintech QA vendor
Domain expertise, the vendor should have demonstrable experience in fintech-specific testing: payment flows, KYC/AML, compliance validation, and financial calculation testing
Security protocols, any vendor with access to your test environment must operate under appropriate security controls, NDAs, and data handling agreements aligned to your compliance obligations
Compliance knowledge, the team working on your account should understand the regulatory requirements your product operates under, not just testing methodology
Communication and integration, the vendor should integrate with your engineering cadence (sprint-based, async feedback, shared tooling) rather than operating as a black box
References in financial services, ask for case studies or references from fintech or financial services clients specifically
Learn how we built a reliable QA system for a growing fintech product
Questions to ask before hiring a QA partner
How do you handle test data that touches customer PII or financial records?
What compliance frameworks has your team worked with, and how do you stay current with regulatory changes?
How do you approach security testing, is it a separate engagement or integrated into your QA practice?
What does your onboarding process look like, and how long before your team is contributing to our sprint?
How do you measure and report the quality outcomes of your work, not just activity, but results?
Red flags to watch for
Vendors who lead with tool names and automation percentages rather than outcomes and risk coverage
No documented experience with compliance-related testing or regulatory frameworks
Inability to clearly describe their test data handling and security protocols
Generic service descriptions with no fintech-specific differentiation
Conclusion
Fintech QA is not a single discipline, it's a layered strategy that spans functional validation, security assurance, compliance verification, performance engineering, and integration testing. Each layer addresses a distinct risk category, and mature fintech organizations treat all of them as non-negotiable.
The teams that cut corners on QA in financial software don't typically see the consequences in the next sprint. They see them six months later in a production incident, a regulatory inquiry, or a data breach disclosure. The cost is always higher than the investment in prevention would have been.
Building a QA function that keeps pace with both the speed of modern fintech development and the demands of the regulatory environment requires the right strategy, the right tools, and, critically, the right expertise. Whether that expertise is built in-house, sourced from a partner, or structured as a hybrid, the investment compounds over time into lower defect rates, cleaner audits, and the kind of operational reliability that fintech users actually trust.
Ready to assess your current fintech QA strategy? DeviQA's team of QA engineers specializes in building QA foundations for financial applications. Get in touch to discuss your specific stack and compliance requirements.
Your dev team need a solid QA partner

About the author
Senior AQA engineer
Ievgen Ievdokymov is a Senior AQA Engineer at DeviQA, focused on building efficient, scalable testing processes for modern software products.