
Written by: Senior AQA Engineer
Ievgen IevdokymovPosted: 13.05.2026
22 min read
A domain-by-domain testing framework for QA engineers and engineering managers building or scaling multi-currency payment features in fintech products.
A currency conversion that's off by 0.01% doesn't look wrong in a test. Multiplied across 50,000 transactions per day, it's a material discrepancy that your finance team flags in the monthly reconciliation, and by then, tracing it back to a rounding implementation decision made six sprints ago is a genuinely expensive exercise.
That's the nature of multi-currency payment testing: the defects that matter most are often the ones that produce the right-shaped output while computing the wrong value. Your test passes. Your logs look clean. The error accumulates silently until something downstream surfaces it.
The scale of the market makes this a high-stakes discipline. The cross-border payments market is now worth over $194 trillion and is forecast to reach $320 trillion by 2032. The volume of money moving through multi-currency systems is large enough that small precision errors have large consequences, and large enough that regulators, auditors, and correspondent banks will find problems you haven't found first.
This guide gives you a structured, domain-by-domain testing framework covering FX accuracy, payment message validation, compliance screening, settlement behavior, error handling, and cross-rail consistency, with specific scenarios at each layer and a pre-launch checklist you can use before opening any new currency corridor.
What you're actually testing when you test multi-currency payments
Multi-currency payment testing is not one testing discipline, it's six. Each layer has different defect types, different testing approaches, and different consequences when it fails.
Most QA programs test one or two layers and call it done. 'We verified the exchange rate displays correctly' covers Layer 2. 'We ran the payment through and it settled' covers Layer 5 in a shallow way. The production failures that make it into post-mortems are almost always in the layers that weren't explicitly covered.
1
FX rate accuracy and precision
Rounding errors, float arithmetic, stale rates
Functional + calculation validation
2
Currency display and locale formatting
Wrong decimals, symbol collision, RTL markets
UI + locale testing
3
Payment message format (ISO 20022)
Field truncation, missing structured data, schema mismatch
Schema validation + integration
4
Sanctions screening under speed constraints
False positive overload, missed party screening
Compliance + performance
5
Settlement timing and reconciliation
Rate lock gaps, fee discrepancy, multi-leg failures
End-to-end + reconciliation
6
Error handling and failure recovery
Silent failures, no-debit-before-reject gaps, duplicate charges
Negative + chaos testing
The key insight: these layers fail independently. A test that validates Layer 5 settlement tells you nothing about Layer 1 FX precision. A Layer 4 compliance test tells you nothing about whether the ISO 20022 message your system generates will be accepted by the correspondent bank. Build your testing program around all six layers, and treat each as a distinct coverage requirement.
Testing area 1: FX rate accuracy and precision
This is where the most invisible production bugs in multi-currency payment testing live, not because FX accuracy is complicated to test, but because teams typically test that a conversion produces a result without testing that it produces the right result, computed correctly, rounded consistently, and applied at the right moment.
Here's what you need to cover:
Floating-point arithmetic, the silent accumulator
Currency amounts must never be stored or calculated using floating-point data types (float, double). IEEE 754 floating-point arithmetic is imprecise for decimal values by design, 0.1 + 0.2 in float doesn't equal exactly 0.3. Across millions of transactions, these imprecisions accumulate into material discrepancies.
Test that your implementation uses decimal arithmetic, a fixed-precision decimal type or an integer-based representation (storing cents, not pounds), for all currency calculations. The simplest test: compute the same conversion in your application and in an authoritative decimal calculator, and compare results to the maximum precision your system supports.
Currency-specific decimal precision
ISO 4217 defines the number of decimal places for every currency. Most are two (USD, EUR, GBP). Japanese Yen and Korean Won have zero. Kuwaiti Dinar and Bahraini Dinar have three. Getting this wrong affects display, calculation, and downstream record-keeping simultaneously.
Test that JPY amounts display as whole numbers, ¥1,000, not ¥1,000.00. A system that adds two decimal places to a JPY amount isn't just displaying wrong; it may be calculating wrong, which means settlements won't reconcile
Test KWD and BHD amounts to three decimal places, a payment for KWD 10.500 and KWD 10.5 are the same value; your system must store, display, and transmit them at the three-decimal scale required by the currency
Test boundary rounding at the final decimal, for a three-decimal currency, how does your system round the fourth decimal place? Document the rule and test that it's applied consistently in both conversion directions
Exchange rate validation: What correct actually means
Test that the rate displayed to a user is the rate applied in execution, not a cached rate from a previous API call. For products that quote a rate and then execute the transaction, test that the rate lock works within the defined validity window and that rate expiry is handled correctly (transaction blocked or re-quoted, not silently executed at an expired rate).
Simulate an exchange rate feed failure and confirm the application's defined fallback behavior executes correctly. Does it block new transactions? Display a stale-rate warning? Default to a spread-protected rate? Whichever behavior is documented, test that it activates consistently, not just that the system doesn't crash.
The most common FX rate testing gap: teams validate that rates are fetched and displayed. They don't test what happens when the rate feed is delayed, returns an error, or returns an outlier rate. That's the scenario where real financial exposure occurs.
Book your QA strategy call
Testing area 2: Currency display, locale, and formatting
Currency display bugs look like UX problems. They're actually financial accuracy problems. A user who misreads an amount because of an incorrect decimal separator or an ambiguous currency symbol is making a financial decision on wrong information, and in regulated markets, that's a disclosure issue, not just an interface issue.
Symbol, code, and locale combinations
Test that the correct ISO 4217 currency code and the correct symbol are displayed for each currency your product supports. The tricky cases: multiple currencies share the dollar sign ($). A Canadian user on a platform that defaults to USD pricing may see $1,000 and interpret it as CAD when the system means USD, a 25% difference.
Test that currency symbols are disambiguated with the ISO code in any context where a user could be exposed to multiple currencies simultaneously. This includes transaction histories, comparison tables, fee breakdowns, and confirmation screens.
Decimal and thousands separators by locale
Germany uses a comma as the decimal separator: €1.234,56. The US uses a period: $1,234.56. For a European fintech with users across multiple countries, these aren't interchangeable. Test currency display in every locale your product supports, not just the development team's default locale.
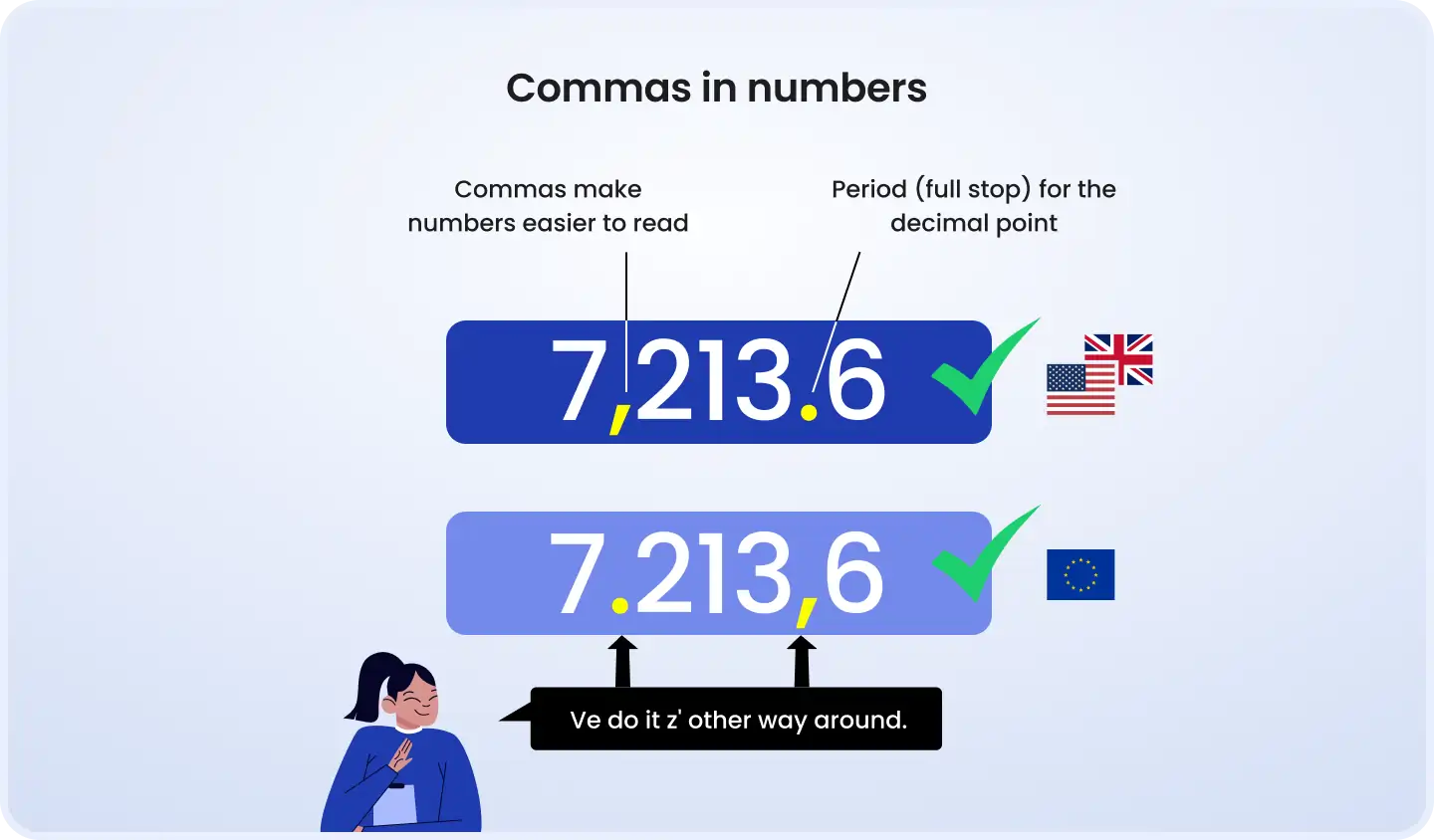
A practical test: take the same amount (for example, €12,345.67) and render it in German (€12.345,67), French (12 345,67 €), and US English ($12,345.67) locales. Confirm that each rendering uses the correct separators, the correct symbol position, and the correct number of decimal places for the locale convention.
Negative amounts, refunds, and adjustments
Test that negative currency amounts, refunds, chargebacks, fee reversals, display and calculate correctly. This sounds simple, but there are specific scenarios that surface problems: a refund on a multi-currency transaction where the original payment was in EUR but the refund is processed in GBP. Which rate applies? The original transaction rate, the current rate, or a defined policy rate?
This is a business rule that must be explicitly defined before it's tested. Once defined, test that it's applied consistently across all refund scenarios, including partial refunds, where the rate calculation must be proportional and traceable to the original transaction record.
Right-to-left markets
For markets using Arabic, Hebrew, or Persian, all of which use right-to-left text direction, the position of currency symbols and the direction of digit groupings may differ from LTR conventions. Test that your currency display renders correctly in RTL contexts, and specifically that the currency symbol appears on the correct side of the amount for each locale.
Testing area 3: Payment message format validation
This is the most current and least-covered dimension of cross-border payment testing in 2025. With the SWIFT ISO 20022 coexistence period now closed, the message format requirements for cross-border payments have changed, and any QA program built against legacy MT format expectations needs to be updated.
ISO 20022 MX messages are now mandatory
From November 22, 2025, all in-scope SWIFT cross-border payment instructions must use ISO 20022 MX format. The relevant messages are pacs.008 for customer credit transfers and pacs.009 for financial institution transfers. If your system generates or processes payment messages, validate them against the MX schema, not the legacy MT format.
The practical shift that matters most for QA: ISO 20022 uses structured XML fields for party data, names, addresses, countries, where MT messages used free-text strings. A name that was acceptable in an MT50 free-text field may fail ISO 20022 structured field validation. Test that your party data mapping produces well-formed, schema-valid MX messages for every payment type you support.
Structured address requirements
From November 2026, unstructured-only address formats will no longer be accepted for most CBPR+ payments. If your system currently stores or transmits customer address data as a single free-text string, test that the structured address fields in your MX messages are populated correctly, with Town/City and Country as separate fields.
Test address data quality across your customer base in your test environment: synthetic customer records with addresses that mix structured and unstructured formats, addresses from non-Latin script countries, and addresses with special characters that may not survive XML encoding. Each of these is a potential message rejection scenario.
IBAN validation by country
Test IBAN validation for every supported destination country's format. IBAN lengths vary from 15 characters (Norway) to 34 (Malta). Each has a country-specific structure and a check digit calculated using MOD-97 arithmetic. An IBAN that passes a basic length check but fails the check digit algorithm will be rejected by the beneficiary's bank, creating a failed payment that requires an investigation workflow.
Build test cases using both valid and deliberately invalid IBANs: wrong length, wrong country prefix, correct format but failed check digit. Confirm that each invalid pattern is rejected at the application layer with a clear error message, not passed to the payment rail to be rejected there.
Rail-specific schema differences
Different payment rails implement ISO 20022 with scheme-specific variations. SEPA, T2, FedNow (US), PIX (Brazil), NPP (Australia), and FAST (Singapore) all use ISO 20022 but have different usage guidelines, field requirements, and validation rules. Test against the specific usage guidelines for each rail you support, not just the base ISO 20022 schema.
ISO 20022 compliance testing is not a one-time validation. Every time you add a new payment corridor or integrate with a new rail, the message format requirements must be validated against that rail's specific usage guidelines and tested end-to-end with a payment that completes, not just validates as schema-conformant.
Testing area 4: Sanctions screening under real-time constraints
International payment QA has a compliance layer that breaks in a specific and predictable way when you add speed: sanctions screening that works correctly in traditional correspondent banking (where you have minutes or hours) stops working correctly in instant payment rails where the entire end-to-end window is 10 seconds.
The SEPA Instant architecture makes this concrete. The EPC's SCT Inst rulebook allocates 5 seconds for the originating PSP, 7 seconds at the CSM level, and 9 seconds maximum end-to-end. There is no room for a blocking per-transaction sanctions check during execution. The compliance architecture is fundamentally different, and your QA must reflect that difference.
Pre-screening workflow testing for instant rails
For instant payment rails, sanctions compliance moves from per-transaction screening to customer-level pre-screening. The compliance model: screen all customers against current sanctions lists before any payment is processed; re-screen immediately when the sanctions list is updated; flag newly sanctioned individuals before their next payment attempt.
Test that this workflow executes correctly:
List update trigger, when a sanctions list is updated, the re-screening process must run within a defined window. Test that the trigger fires correctly and that re-screening covers the full customer base, not just new sign-ups
Flagging and hold workflow, a customer flagged by re-screening must have payment capability suspended until the flag is reviewed. Test that the suspension is applied before any payment attempts, not after
False positive review workflow, test the entire resolution path for a flagged account that is determined to be a false positive: flag created, review triggered, false positive confirmed, account reinstated, payment processing resumed. Each step must be traceable
Coverage across all payment parties
Sanctions screening must cover all parties in the payment chain: originator, beneficiary, and intermediary institutions. The most commonly missed coverage gap: in ISO 20022 cover payment scenarios, both the interbank instruction (Sequence A) and the underlying customer details (Sequence B) must be screened independently.
Test that your screening implementation explicitly covers all required party fields, not just the primary beneficiary name. A payment that screens the beneficiary but not the ordering customer is a compliance failure even if the beneficiary is clean.
Calibrating and testing the false positive rate
Industry estimates place sanctions alert rates at 5–10% of transactions, with the vast majority being false positives. A threshold that generates 8% alerts against a high-volume payment platform creates an operational backlog that is itself a compliance risk, reviewers overwhelmed with false positives are less likely to give genuine alerts adequate attention.
Test the screening threshold against a realistic synthetic transaction dataset: measure the false positive rate at the current threshold, test the rate at thresholds one step above and below, and document the operational impact of each setting. The right threshold is not the one that minimizes false positives, it's the one that balances detection accuracy with review capacity.
Testing area 5: Settlement timing and reconciliation accuracy
Settlement in cross-border payment testing is where FX precision errors, fee calculation gaps, and multi-leg failure scenarios accumulate into real financial discrepancies. Most QA programs test that payments settle, not that they settle correctly.
Rate lock timestamp behavior
When does the exchange rate lock for a conversion? At payment initiation? At the first leg of settlement? At final settlement? The answer is a business rule that must be explicitly defined, implemented, and then tested.
Test that the rate applied in the final transaction record matches the rate locked at the documented timestamp. Test the timestamp recording specifically: is it stored as UTC or local time? Is it precise enough (milliseconds, not seconds) to be unambiguous? Is it visible in the audit trail at the level of detail that a dispute investigation requires?
The edge case that exposes most rate lock implementations: a payment initiated at the close of a trading day where the rate changes between initiation and settlement the following morning. Test that the locked rate is preserved across this boundary, not silently overwritten by the settlement-time rate.
Multi-currency reconciliation testing
If your product maintains balances in multiple currencies, test that balance updates remain consistent after a conversion transaction: the debit in the source currency and the credit in the destination currency must balance at the locked exchange rate, with no residual value unaccounted for.
A practical reconciliation test: initiate a series of conversion transactions between two currencies, then sum all debits and credits in each currency and verify that the totals are consistent with the applied exchange rates. Any discrepancy, even a fraction of a penny per transaction, indicates a calculation defect that will accumulate at scale.
Fee transparency: Quote to settlement
Test that the fees shown at quote time match the fees deducted at settlement. FX fees, correspondent bank charges, and intermediary fees must be disclosed before the transaction is authorized, that's a regulatory requirement in most jurisdictions, and the disclosed amounts must match what's actually deducted.
The failure mode: a fee that's correctly calculated at quote time using the current rate but recalculated at settlement using the settlement rate, producing a different amount. This is a common implementation defect in platforms where fee calculation and rate locking are handled by separate services.
Value date and cut-off window testing
Many payment rails have cut-off times that affect the settlement value date. A SEPA Credit Transfer initiated at 23:50 may settle on a different value date than one initiated at 08:00 the same day. Test value date calculation for all supported payment corridors, specifically at the boundaries of cut-off windows, and confirm that the value date is correctly communicated to the customer before they authorize the transaction.
Testing area 6: Error handling and failure recovery
Error handling is the test category most teams write last, and the one most production failures come from in multi-currency payment systems. The complexity comes from the number of independent systems involved: the FX rate feed, the payment rail, the correspondent bank, the customer's account, and your own backend can all fail independently, and each failure mode has different recovery requirements.
Exchange rate feed failure
Simulate the FX rate provider going unavailable during active transaction processing. What does your application do? The three possible behaviors each have different implications:
Block new transactions, zero financial risk, but high customer friction. A payment platform that rejects all conversions during a 30-minute rate feed outage creates customer-facing failures during that window
Display stale rate with disclosure, acceptable for many use cases if the staleness window is bounded and disclosed, but must be tested: is the disclosed rate actually the rate used in execution?
Default to a spread-protected fallback rate, the most user-friendly option, but requires testing that the spread calculation is correct and that the fallback triggers and terminates correctly
Document the intended behavior, then test that it executes consistently, not just when the rate feed returns a clean error, but when it returns a timeout, a malformed response, or an outlier rate that falls outside a reasonable validation range.
Book a strategic QA consultation
Unsupported currency corridor rejection
Test that payment attempts to unsupported currency corridors or destination countries are rejected before funds are debited from the customer's account. A payment that debits the source account and then fails because the destination currency isn't supported requires a reversal workflow, which has its own timing, accuracy, and customer communication requirements.
Test the specific sequence: attempt a payment to an unsupported corridor, confirm no debit occurs, confirm the rejection message is clear and actionable, and confirm that the account balance is unchanged. Then test the edge case where a corridor was previously supported and has been removed, an in-flight payment that enters processing before the corridor was disabled.
Duplicate transaction prevention
In multi-currency payment flows, network timeouts frequently trigger duplicate payment attempts. A user who sees their payment 'stuck' may resubmit. A mobile app that retries on reconnection may resubmit. Test idempotency specifically across exchange rate movement scenarios: if a duplicate request arrives after the original rate has expired, which rate is applied, and does the system prevent the duplicate from executing as a new transaction?
Refund rate policy
A refund on a cross-border transaction can use the original transaction rate, the current market rate, or a defined policy rate. Each choice has a different outcome for the customer. Test that your refund rate policy, whatever it is, is applied consistently across all refund scenarios: full refunds, partial refunds, delayed refunds where the rate may have moved significantly, and refunds initiated by the merchant rather than the customer.
Your multi-currency payment testing checklist: before you go live in a new market
Use this checklist before enabling any new currency or opening any new payment corridor. Every item maps to a specific failure mode that has caused production incidents in real fintech products.
☐
Decimal precision per ISO 4217 (JPY = 0, KWD = 3)
FX Accuracy
Incorrect amounts displayed and recorded
Critical
☐
Rounding rule consistent in both conversion directions
FX Accuracy
Systematic gain/loss on high-volume conversion
Critical
☐
Rate source timestamp: displayed rate = executed rate
FX Accuracy
Customer pays wrong rate; dispute risk
Critical
☐
Decimal arithmetic confirmed (no float in currency calc)
FX Accuracy
Accumulating precision errors at scale
Critical
☐
Currency symbol disambiguated with ISO code
Display
User misreads transaction amount in shared-symbol currencies
High
☐
Decimal and thousands separator validated per locale
Display
Amount misread by users in non-default locales
High
☐
RTL display tested for Arabic, Hebrew markets
Display
Broken layout; symbol on wrong side of amount
Medium
☐
Negative amounts (refunds) formatted correctly
Display
Confusing customer statements; accounting errors
High
☐
ISO 20022 MX schema validated for each rail
Message Format
Payment rejected at correspondent bank
Critical
☐
Structured address fields populated (not free-text)
Message Format
Non-compliant from Nov 2026; payment delays
High
☐
IBAN validation: format and check digit per country
Message Format
Payment rejected; expensive investigation
Critical
☐
Sanctions coverage: all parties (not just beneficiary)
Compliance
Regulatory violation; fine exposure
Critical
☐
Pre-screening workflow for instant payment rails
Compliance
10-second window violated; payment blocked
Critical
☐
False positive rate measured at current threshold
Compliance
Alert fatigue; genuine flags missed
High
☐
Rate lock timestamp defined, implemented, audited
Settlement
Customer disputes rate applied at settlement
Critical
☐
Multi-currency balance reconciles post-conversion
Settlement
Financial leakage; reconciliation failure
Critical
☐
Quote-time fees match settlement-time deductions
Settlement
Regulatory disclosure violation; disputes
High
☐
Value date calculation at cut-off window boundaries
Settlement
Unexpected settlement delay; SLA breach
High
☐
Duplicate transaction prevention across rate movement
Error Handling
Double charge to customer
Critical
☐
Refund rate policy: original vs. current rate
Error Handling
Customer receives wrong refund amount
High
☐
Unsupported corridor rejected before debit
Error Handling
Failed debit requiring reversal workflow
Critical
Where to start with your multi-currency testing program
If you're building multi-currency payment features for the first time, start with Layer 1, FX precision. The floating-point issue alone is worth a focused engineering review before any testing begins. If your codebase uses float or double for currency arithmetic anywhere in the conversion pipeline, that's a defect before any test is written.
If you're auditing an existing multi-currency QA program, map your current test coverage against the six layers above. Most teams find they have reasonable Layer 2 coverage (display testing) and some Layer 5 coverage (settlement flows), with significant gaps in Layers 3 and 4, ISO 20022 message validation and sanctions screening under timing constraints.
The ISO 20022 cutover is the most urgent current item for any team operating SWIFT cross-border payments. The coexistence period has ended. If your integration tests still reference MT message formats, they're testing against a standard that no longer applies for in-scope SWIFT traffic.
The six testing areas above aren't sequential, they need to run in parallel as you expand markets, add currencies, and integrate payment rails. The cross-border payment testing program that keeps pace with your product roadmap is one that has coverage built into each layer as a standing discipline, not assembled under pressure before each market launch.
Expanding to new markets or adding multi-currency features to your fintech product? DeviQA works with fintech teams on payment testing strategy, from FX precision validation and ISO 20022 compliance to sanctions screening test design and cross-border settlement reconciliation testing. Get in touch to discuss your currency expansion roadmap.
Talk to a QA expert

About the author
Senior AQA engineer
Ievgen Ievdokymov is a Senior AQA Engineer at DeviQA, focused on building efficient, scalable testing processes for modern software products.