
Written by: Senior AQA Engineer
Ievgen IevdokymovPosted: 14.05.2026
25 min read
A lifecycle-based testing framework for QA engineers and engineering managers integrating or maintaining payment gateway functionality in fintech and e-commerce products.
Most teams test payments like a feature. They're wrong. Payments are where your product becomes revenue. And 67% of users walk away when something breaks there. Not crashes. Friction: confusing errors, failed retries, 3DS loops, silent timeouts, missing confirmations.
In testing, everything looks fine. The sandbox passes. The flow is "green." But users don't live in your sandbox. They switch networks. Banks interrupt flows. Real conditions break what tests don't catch.
Here's the problem: you don't control the payment gateway. And the gap between sandbox and production is where most bugs live.
This guide gives you a lifecycle-based testing framework organized around the actual stages of a payment transaction, from checkout initiation through webhook delivery and post-purchase handling. Not by testing type, but by what's happening in the payment flow at each moment and what can go wrong there.
Why most payment gateway testing misses the real problems
Standard payment integration testing hits the happy path and a handful of obvious failure modes. Valid card, sufficient funds, approved, test passes. Invalid card number rejected, test passes. What's missing is everything in between: the ambiguous states, the adversarial scenarios, and the asynchronous failure modes that functional testing doesn't reach.
Here are the six gaps that cause most production payment failures, and why teams consistently miss them:
Hard vs. soft decline handling
Teams test 'payment declined' as one scenario
Retried hard declines trigger card blocks; soft declines show permanent-failure messages to users who could retry
Business logic bypass (price tampering)
Redirect integrations are tested functionally, not adversarially
Attacker submits modified POST price to gateway; order processed at discounted amount
Success-page force browsing
No one tests what happens without a valid payment
User navigates directly to confirmation URL; order ships without payment being collected
Webhook idempotency
Webhook testing covers delivery, not duplicate delivery
Webhook retry triggers double order fulfillment, double inventory deduction, or double charge
3DS challenge flow on mobile
Frictionless flow is tested; challenge flow is not
Users requiring challenge are stranded in authentication loop; real abandonment event
Gateway timeout state management
Happy path and clear-fail are tested; ambiguous timeout is not
Timeout creates unknown transaction state; user sees error but payment may have been captured
The common thread across all six: they require testing scenarios that don't feel like standard test cases. Force-browsing to a success page, replaying a webhook twice, manipulating a POST price, these feel like attack scenarios or infrastructure tests. They are. And they need to be in your payment gateway QA coverage before they're in your production incident log.
Stage 1: Checkout initiation, before the payment form even appears
Payment gateway testing doesn't start at card submission. It starts at checkout initiation, because errors at this stage create broken sessions that produce confusing downstream failures, and because the most serious business logic vulnerabilities in payment integrations exist here, not in the card processing layer.
Cart amount integrity between application and gateway
In redirect and cross-domain POST integrations, the order amount is transmitted to the payment gateway as part of the redirect or form data. In many implementations, this amount exists as a modifiable field before it reaches the gateway. Test it adversarially: submit a checkout session with a tampered POST amount, lower the total by modifying the form data before submission, and confirm the gateway or your application rejects the discrepancy.
This is an OWASP-documented vulnerability in hosted payment gateway integrations. The correct defense is server-side amount validation: your backend generates a session token tied to the canonical order amount, and the gateway validates against that token, not the client-transmitted amount. If your integration relies on client-side amount transmission without server-side validation, this test will reveal it.
The business logic bypass test most teams skip
In redirect-based gateway integrations, the payment flow works like this: user completes payment on the gateway's page, gateway redirects to your success URL with a result parameter. The critical question is whether your application validates the payment result server-side, via an API call to the gateway, before processing the order. Or does it trust the client-side redirect parameter?
Test this explicitly: after the gateway redirect step, manually navigate to your success URL (success.php, /order/confirmed, or equivalent) with a valid order ID, without completing a payment on the gateway. If your application processes the order, fulfills it, and sends a confirmation email, your integration has a business logic bypass. The fix requires a server-side payment status verification call before any order processing occurs.
PCI DSS scope and checkout security
Confirm that all checkout pages load over HTTPS without exception, including pages that don't themselves contain payment forms but redirect to them. Test that card input fields are served from the appropriate scope: a gateway-hosted iframe or redirect satisfies SAQ A with 22 requirements; a self-hosted form puts you in SAQ D scope with 329 requirements.
Check browser developer tools during checkout: card data must not appear in page source, local storage, session storage, or network request payloads outside the gateway's own secure endpoints. This test is often assumed to be covered by the gateway implementation. It frequently isn't, especially when custom analytics scripts or tag managers have been added that capture form field values.
Book your QA strategy call
Stage 2: Card authorization, the test scenarios that actually matter
Authorization is the stage most payment gateway QA programs test most thoroughly, and still miss the scenarios that drive support volume. The happy path is the least interesting authorization test you can write.
Testing across card brands
Test successful authorization across every supported card scheme: Visa, Mastercard, Amex, Discover, and any regional schemes your market requires. Gateway behavior varies subtly by scheme, error response formats differ, AVS field handling differs, and authorization hold expiry windows differ. A gateway that handles Visa correctly may have a formatting issue in Amex responses that only surfaces when an Amex-specific field is present.
Hard vs. soft declines: The distinction that changes your recovery logic
Not all declines are equal, and treating them equally is one of the most common sources of checkout conversion loss.
Hard declines are permanent rejections: stolen card, invalid card number (error 2005), card reported as lost. Your application must not retry a hard decline. Retrying a hard decline risks triggering velocity checks at the issuer, which can result in the card being temporarily blocked, a worse outcome than the initial decline. Test that hard decline codes produce an error message that guides the user to try a different card, not to try again.
Soft declines are temporary rejections: insufficient funds, card velocity limit exceeded, do not honor (which often resolves after a short window). Soft declines can be retried, but retry timing and message framing matter. Test that soft decline codes produce messages that indicate a temporary issue ('your card couldn't be processed at this time') rather than a permanent failure ('your card has been declined'). The difference in conversion rate between these two messages is measurable.
Test the specific decline codes your gateway documents: insufficient funds, expired card, invalid CVV, card reported lost/stolen, transaction not permitted for card type, exceeded withdrawal limit, do not honor. Each should trigger a different application response, different user message, different retry eligibility, different log entry.
AVS mismatch handling
AVS (Address Verification System) compares the billing address provided at checkout against the address on file with the card issuer. Most gateways return an AVS result code alongside the authorization response. Your configured AVS policy determines what happens with mismatches, and that policy should be explicitly tested.
A full AVS mismatch (both address and zip don't match) on a high-value transaction is a different risk profile from a zip-only mismatch on a low-value transaction. Test that your AVS policy fires correctly for each mismatch type, and that the application response, accept, decline, or flag for review, matches the documented policy. This is a configuration test, not just a functional test.
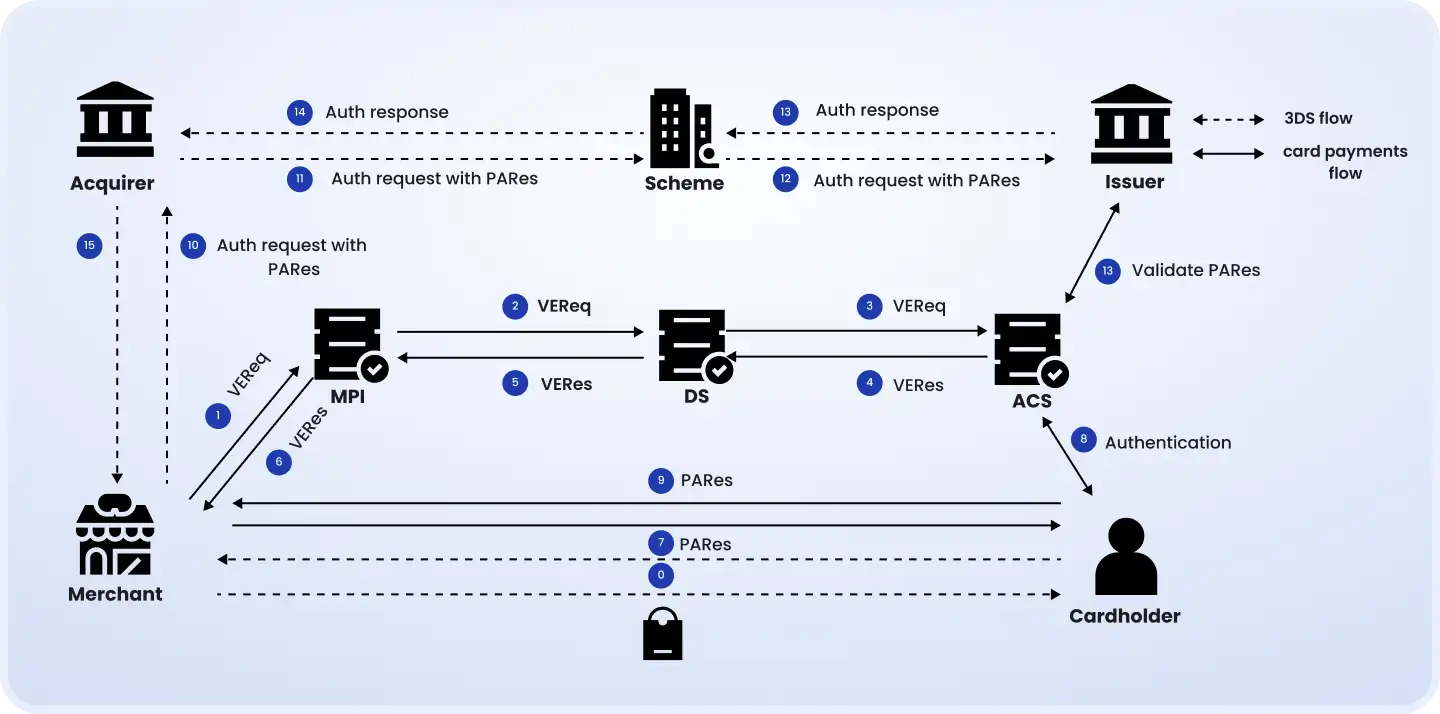
Stage 3: 3DS authentication, testing both flows and all failure states
3DS2 is now the authentication standard for card-not-present transactions under PSD2. Testing it thoroughly matters for two reasons that go beyond compliance.
First, economics: successful 3DS authentication shifts chargeback liability from the merchant to the card issuer. Second, the Visa VAMP policy change from April 2025 changed how fraud rates are calculated, fraud chargebacks that were previously manageable through automated dispute resolution now count toward your fraud rate regardless of resolution method. A properly implemented and tested 3DS flow is now a direct revenue protection measure.
The frictionless flow
The 3DS2 frictionless flow authenticates the transaction silently, the issuer's risk scoring determines the transaction is low-risk, and authentication completes without user interaction. 85% of well-implemented 3DS2 transactions complete frictionlessly when rich device data is provided.
Test that the frictionless flow completes without any 3DS UI appearing to the user, that the ECI (Electronic Commerce Indicator) value in the authorization request is correctly populated (05 for fully authenticated), and that the liability shift is correctly attributed. The ECI value is the evidence that liability has shifted to the issuer, an incorrect ECI means you bear chargeback liability even on authenticated transactions.
The challenge flow, the one that's actually tested by real users
When a transaction risk scores higher, the issuer requires a challenge: an OTP sent to the cardholder's phone, a biometric prompt through the banking app, or a redirect to the issuer's authentication page. This is the flow that most QA coverage ignores, and the one that users encounter when they buy from a new device, make an unusually large purchase, or shop from an unfamiliar location.
Test the full challenge sequence on both desktop and mobile: the challenge prompt renders correctly and is clearly associated with the transaction, the user can complete the OTP or biometric step, the authentication result is correctly passed back to your application, and the authorization proceeds after successful completion. On mobile specifically, test banking app redirect challenges where the user leaves your app, authenticates in their banking app, and returns, the session must survive this navigation.
3DS failure states and fallbacks
Test every way 3DS authentication can fail: wrong OTP entered, OTP timeout, user cancels the challenge, issuer 3DS system unavailable. Each state must produce a specific response, a user message that explains what happened and offers a path forward (try again with the same card, try a different card, contact the bank), rather than a generic payment error.
Test the 3DS system unavailability scenario explicitly: when the issuer's 3DS endpoint doesn't respond within your configured timeout, does your integration fall back according to your policy? Falling back to non-authenticated authorization increases fraud risk but avoids blocking legitimate transactions. This decision is a configuration your team makes, and it must be tested to confirm it executes correctly.
SCA exemption paths
PSD2 permits specific transactions to bypass SCA: low-value transactions under €30, transactions with a trusted beneficiary, corporate card transactions, and recurring transactions with consistent amounts after the initial SCA-authenticated setup. Test that your implementation correctly requests these exemptions where eligible, and that exemption refusal by the issuer (who can override an exemption request and require a challenge) falls back to the challenge flow gracefully rather than causing a transaction failure.
Stage 4: Tokenization and saved payment methods
Card tokenization testing is a distinct layer from authorization testing. You're validating not just that a payment works, but that the token lifecycle, creation, storage, use, and deletion, is correctly implemented, secure, and compliant.
Token creation and PCI DSS scope
After a successful first payment, confirm the token is created and stored correctly. Then test what didn't get stored: search your application logs, debug output, database records, and API response logs for any occurrence of the raw card number. Raw card data must not appear anywhere in your application infrastructure, only the gateway-issued token. A single log line that includes a card number puts your entire logging infrastructure in PCI DSS scope.
This is a security test that requires intentionally looking for data that shouldn't be there, not just confirming that the token exists. Run it after every significant change to your payment flow, logging configuration, or API integration.
Token-based subsequent payments and cross-account security
Test that a payment using a stored token completes correctly without requiring card re-entry. Then test the security boundary: a token stored for Customer A must not be usable by Customer B, even if Customer B knows Customer A's token value. Test this explicitly by attempting to initiate a payment using another account's token, this should return a specific error, not process the payment.
Expired card handling and network tokenization
Network tokenization, where Visa or Mastercard manages card updates automatically behind the token, means a gateway token may continue to work after the physical card's printed expiry date, because the network has silently updated the underlying card details. Test that expired card handling is correct for both network tokens (which auto-update and should continue to work) and standard gateway tokens (which may not auto-update and should return an appropriate expired card error).
The failure mode to test: a customer's card expires, network tokenization is not in place, and your application attempts to charge the expired card token without handling the failure. This should trigger an appropriate message and offer the customer a path to update their payment method, not fail silently or produce a confusing generic error.
Token deletion under GDPR
When a user exercises their GDPR right to erasure, stored payment tokens must be deleted. Test that token deletion propagates through your system: the token is removed from your database, the deletion is signaled to the gateway, and any subsequent payment attempt using the deleted token returns an appropriate error rather than attempting to process. A deleted token that can still be charged is both a GDPR violation and a security issue.
Book your QA strategy consultation
Stage 5: Post-payment webhooks, where most integrations actually break
Here's a production failure mode that appears in almost no payment gateway testing guide: the authorization succeeds, the gateway processes the payment, and your application never knows. No webhook arrived. Or it arrived twice. Or it arrived out of order with the refund webhook.
Webhooks are the asynchronous communication channel between the gateway and your application after the user interaction ends. They can be delayed, retried, delivered out of order, and duplicated. Your application needs to handle all of these scenarios correctly, and most applications have tested exactly one of them: the successful delivery of a single webhook, once, in order.
The idempotency test your integration probably doesn't have
Gateways retry webhooks when your endpoint returns a timeout or a 5xx response. This means the same payment webhook may arrive twice, and if your webhook handler isn't idempotent, it will process the same payment event twice. Two order fulfillments, two inventory deductions, two confirmation emails, or, in worst cases, two charges.
Test this explicitly: simulate webhook retry delivery by replaying the same webhook payload twice to your endpoint. The second delivery must produce no side effects. The correct implementation uses the gateway's event ID as a deduplication key, check if the event has already been processed, and skip if it has. If your webhook handler doesn't implement this check, duplicate delivery in production will eventually produce a duplicate order.
Webhook signature verification, a security test, not just functional
Every major payment gateway provides a mechanism for webhook signature verification: a secret key used to sign the payload, which your endpoint verifies before processing. Test that your endpoint correctly rejects webhooks with invalid or missing signatures, because an endpoint that accepts unsigned webhooks can receive a fake payment.success event, causing your application to fulfill an order without any payment being collected.
Test this by sending a webhook payload with a tampered signature and confirming a 401 or 403 response. Then test with a valid signature on a tampered payload, the signature won't match the tampered content, and the rejection must fire. Both tests confirm that signature verification is correctly implemented, not just present in the code.
Delayed and out-of-order webhook delivery
Simulate a webhook arriving significantly after the transaction: the user completes payment, returns to your application, and sees a 'payment processing' status for 20 minutes before the webhook finally arrives. Does your application correctly handle the pending state during the delay? Does it incorrectly mark the order as failed and send a failure notification, only to then process the late webhook and create a confusing second notification?
Test out-of-order delivery by simulating a refund webhook arriving before the corresponding payment webhook. Your application must handle this gracefully, either queuing the refund event until the payment event arrives, or correctly processing the refund against a payment it hasn't yet seen in its own database.
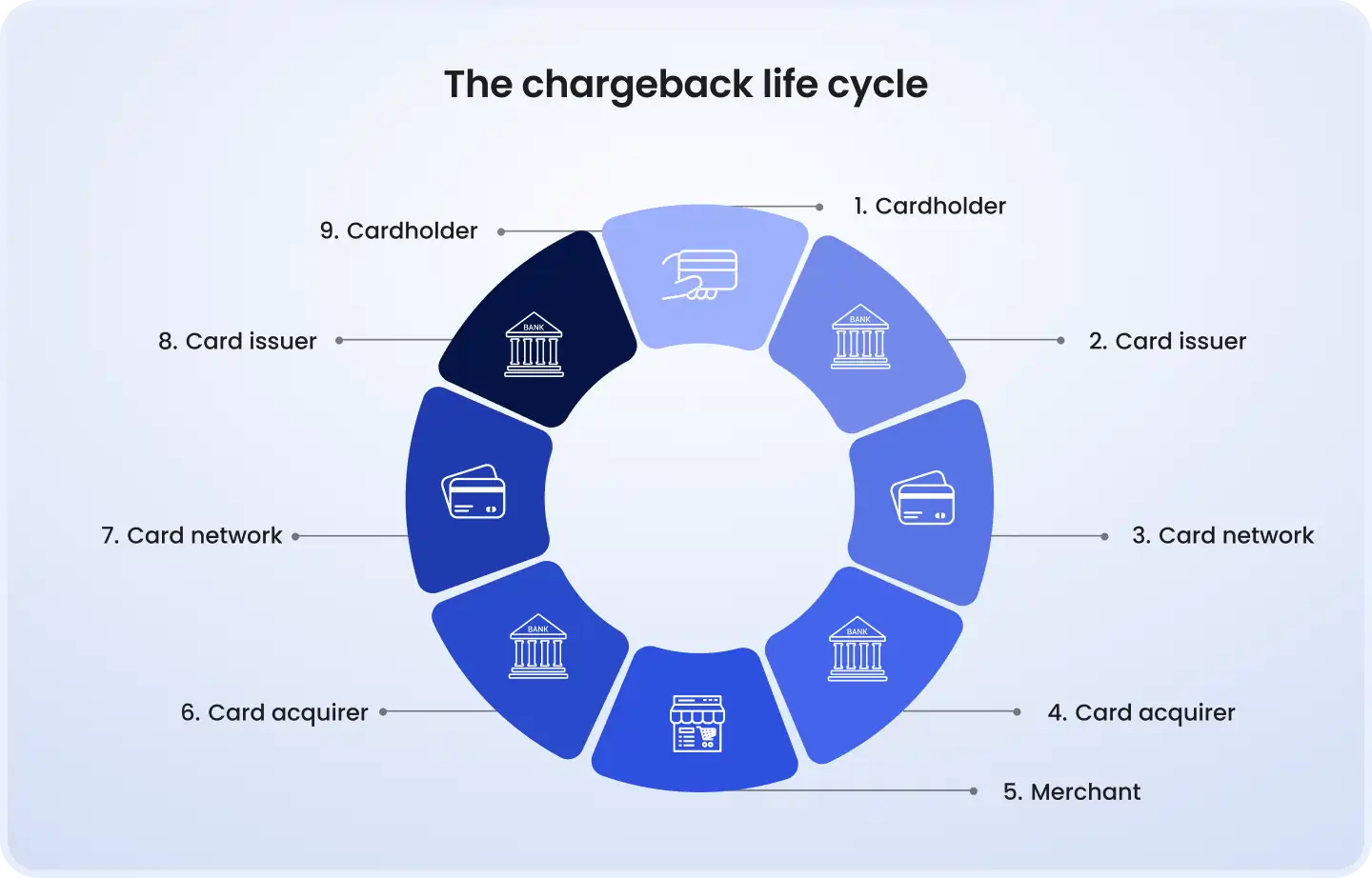
Stage 6: Refunds, chargebacks, and partial captures
The post-purchase payment lifecycle is where compliance requirements and customer trust intersect. A refund that processes correctly in the gateway but fails to update your order management system creates a support problem. A chargeback dispute you can't respond to within the window is a guaranteed loss.
Refund testing
Test full refunds across all supported payment methods, refund behavior varies by method (card refunds to the original card, wallet refunds to the wallet balance, bank transfer refunds require separate bank details). Confirm the refunded amount can never exceed the original transaction amount; this is a validation your application must enforce independently, not rely on the gateway to catch.
Test multiple partial refunds against the same transaction. A customer returns two of three items at different times, each generates a partial refund against the original transaction. Test that your application correctly tracks the cumulative refunded amount and prevents subsequent refunds from exceeding the original total. Then test the time boundary: a refund initiated against a transaction that has already been fully refunded must fail with a clear error, not attempt to process.
Chargeback handling in the 2026 landscape
Visa's VAMP policy change from April 2025 raised the stakes for chargeback management: fraud disputes that were previously resolvable through automated dispute resolution channels now count toward your fraud rate calculation regardless. The safety net of automated chargeback resolution for fraud reason codes is no longer available at the same scale.
Test that chargeback disputes are correctly received through the gateway's webhook, that the dispute metadata, reason code, original transaction details, response deadline, is correctly captured in your system, and that the dispute is routed to the appropriate review queue before the response window closes. Dispute windows are typically 20–45 days; a dispute that sits unrouted in a queue past its deadline is an automatic loss.
Partial captures
A partial capture completes only a portion of an authorized amount, common in scenarios where the final total isn't known at authorization time, such as split shipments or services where usage determines the final charge. Test that partial capture correctly adjusts the settled amount, that the remaining authorized-but-uncaptured amount is correctly voided (not left as an open authorization on the customer's card), and that the customer statement reflects only the captured amount.
Stage 7: Performance and failure recovery under load
Functional payment gateway testing tells you whether your integration works. Performance testing tells you whether it holds when the conditions that actually stress payment systems occur: Black Friday traffic, end-of-month payroll spikes, real-time event ticket sales. Black Friday 2024 saw payment volumes increase 340% over average daily volume. An integration that handles 1,000 transactions per hour smoothly may create timeouts, connection pool exhaustion, and cascading failures at 3,400 per hour.
Gateway timeout state management
The timeout scenario is the most dangerous ambiguous state in payment processing: your application sends a payment request to the gateway, the gateway doesn't respond within your configured timeout window, and you don't know whether the payment was captured or not. The wrong response, marking the transaction failed and telling the user to try again, risks a double charge. The correct response is to put the transaction in a pending state, poll the gateway for the transaction status, and resolve the state before taking any further action.
Test this explicitly using your gateway's sandbox timeout simulation: trigger a timeout response, confirm the application puts the transaction in a pending state without user-facing error, and confirm the status resolution polling fires correctly. Then test what the user sees during the pending window, the checkout UI must communicate that processing is in progress, not show an error or completion state that doesn't yet reflect reality.
Connection pool behavior under load
Under peak load, does your application correctly queue gateway requests rather than opening unlimited simultaneous connections? Unlimited connections to a gateway API create gateway-side rate limiting, which produces errors that look like transaction failures to users, but are actually infrastructure failures in your own connection management. Load test your payment integration specifically, not just your application generally, to confirm that payment processing remains stable under the volumes your product is expected to reach.
Latency communication to the user
Test what the user experience looks like when gateway response time increases from its normal 300–500ms to 2–3 seconds under load. Does your checkout UI communicate that processing is in progress? Does it look frozen? A payment form that shows no activity for 3 seconds will trigger double-submission attempts from users who think the first click didn't register, which creates duplicate payment requests that your idempotency handling must absorb.
The complete payment gateway testing checklist
Every item below maps to a specific production failure mode. Use this before launching a new payment integration, before any significant gateway configuration change, and as the basis for your automated regression suite.
☐
Cart amount integrity: tamper POST price to gateway
Initiation
Price manipulation, order at wrong amount
Critical
☐
Success-page force-browse without valid payment
Initiation
Order ships without payment collected
Critical
☐
HTTPS on all checkout pages; card data absent from source
Initiation
PCI DSS scope violation; card data exposed
Critical
☐
Payment method availability per locale and currency
Initiation
Method shown but fails at gateway for region
High
☐
Successful authorization, all supported card brands
Authorization
Undetected brand-specific gateway behavior
Critical
☐
Hard decline codes: invalid card, stolen card
Authorization
Hard declines retried; card blocked; fraud flag
Critical
☐
Soft decline codes: insufficient funds, velocity limit
Authorization
Soft declines show permanent failure; lost retryable sale
High
☐
AVS mismatch handling per configured policy
Authorization
High-value fraud passes; legitimate orders blocked
High
☐
3DS frictionless flow: ECI value, no UI shown
3DS
Incorrect liability shift claimed; chargeback exposure
Critical
☐
3DS challenge flow: full UX on desktop and mobile
3DS
Challenge-required users stranded; real abandonment
Critical
☐
3DS failure states: timeout, cancel, wrong OTP
3DS
Users permanently blocked after authentication failure
High
☐
3DS exemption paths: low-value, recurring, trusted beneficiary
3DS
Excessive SCA friction; conversion loss
High
☐
Token creation: raw card absent from logs and database
Tokenization
PCI DSS violation; card data stored in scope
Critical
☐
Token-based subsequent payment
Tokenization
Saved payment method fails; customer re-entry required
High
☐
Token deletion on account erasure (GDPR)
Tokenization
Deleted token still charges; regulatory violation
High
☐
Expired card token behavior
Tokenization
Silent charge attempt on expired card
Medium
☐
Successful payment webhook triggers fulfillment
Webhooks
Order paid but not fulfilled
Critical
☐
Webhook idempotency: duplicate delivery handled
Webhooks
Double fulfillment, double charge
Critical
☐
Webhook signature verification
Webhooks
Fake payment-success injected; order shipped without payment
Critical
☐
Delayed webhook: pending state during gap window
Webhooks
User sees payment failed; order not processed
High
☐
Full refund: cannot exceed original amount
Refunds
Over-refund; financial leakage
Critical
☐
Partial refund: multiple partials don't exceed total
Refunds
Cumulative over-refund; accounting discrepancy
High
☐
Chargeback dispute routing and evidence deadline
Chargebacks
Missed dispute window; guaranteed loss
High
☐
Gateway timeout: transaction state resolution
Performance
Unknown state; user error + possible double charge
Critical
☐
Payment volume under peak load (3x average)
Performance
Timeout cascade; production payment failures at volume
High
What to automate vs. what needs manual attention
Not all payment gateway tests are equally suited to automation. Some require real device conditions, real issuer behavior, or adversarial creativity that automated test runners can't replicate. Here's the practical split:
Happy path: all supported card brands and payment methods
3DS challenge flow on real mobile devices (banking app redirect, biometric)
All documented hard decline codes and application responses
Business logic bypass: success-page force-browse, POST price tampering
Soft decline codes and retry logic behavior
Chargeback dispute response workflow end-to-end
Webhook idempotency and signature validation
Gateway failure simulation under peak load conditions
Amount integrity: application total vs. gateway-received amount
PCI DSS scope: card data in logs, network requests, browser storage
Token creation, retrieval, and post-deletion error response
3DS exemption path validation across card issuers
Full and partial refund amount validation
AVS mismatch policy review against current fraud patterns
The boundary rule: automate anything with a deterministic expected output that you need to validate on every deployment. Reserve manual testing for anything that requires real device conditions, real bank behavior, or an attacker's decision-making logic. Both categories are required, neither replaces the other.
Where to start with your payment gateway testing program
If you're building a new payment gateway integration, start with the business logic bypass tests before you test anything else. Force-browse to the success page without a payment. Tamper with the POST price in a redirect integration. These tests take 30 minutes and reveal the most serious security and financial exposure before any other testing begins.
If you're auditing an existing payment gateway QA program, map your current test coverage against the seven lifecycle stages above. Most teams find complete coverage in Stages 2 (authorization) and 6 (refunds), reasonable coverage in Stage 1 (checkout), and significant gaps in Stages 3 (3DS challenge flows), 5 (webhook edge cases), and 7 (performance under load).
The 2025 changes, Visa VAMP's new fraud rate calculation and 3DS2's frictionless authentication as the standard, mean that gaps in 3DS coverage and chargeback handling carry higher financial consequences than they did previously. If your test suite predates these changes, it has blind spots that are now more expensive than they used to be.
Every stage of the payment lifecycle from checkout initiation to final confirmation is a potential failure point. The ones that cause real production incidents aren't the obvious functional failures, they're the business logic bypasses, the webhook edge cases, the decline code handling differences, and the 3DS challenge flows that nobody thought to test because the sandbox didn't require them.
Building or auditing a payment gateway integration? DeviQA's QA team works with fintech and e-commerce teams on end-to-end payment testing, from sandbox configuration and business logic security testing to 3DS flow coverage, webhook validation, and production load testing. Get in touch to discuss your integration.
Your dev team need a solid QA partner

About the author
Senior AQA engineer
Ievgen Ievdokymov is a Senior AQA Engineer at DeviQA, focused on building efficient, scalable testing processes for modern software products.